
I had so much fun designing and executing this attack, from hardware to software! Huge thanks to @thezdi.bsky.social for introducing such devices and attack vectors into the contest!
23.01.2025 19:50 — 👍 10 🔁 3 💬 0 📌 0@fidgetingbits.bsky.social

I had so much fun designing and executing this attack, from hardware to software! Huge thanks to @thezdi.bsky.social for introducing such devices and attack vectors into the contest!
23.01.2025 19:50 — 👍 10 🔁 3 💬 0 📌 0"founder of Aziumuth"
23.12.2024 01:54 — 👍 1 🔁 0 💬 0 📌 0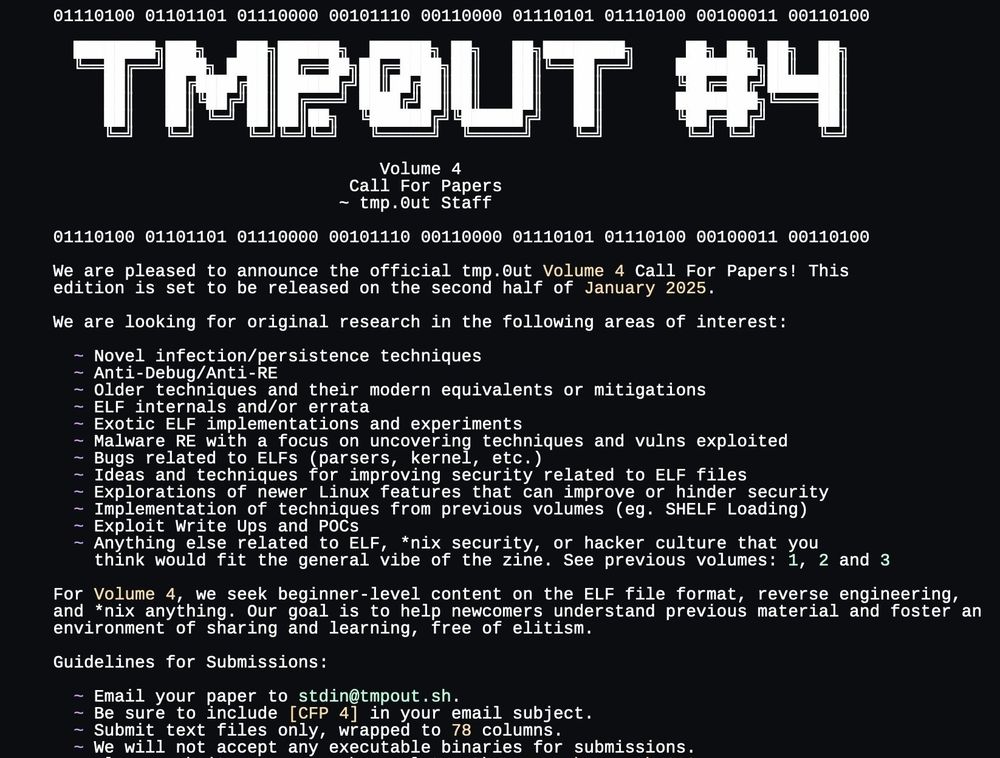
We are extending our call for papers to January 1, 2025!
We are now targeting an end of January release.
If you have any Linux/ELF related research, projects, or papers, we would love to publish them!
Huge thank you to everyone who has already submitted!
tmpout.sh/blog/vol4-cf...
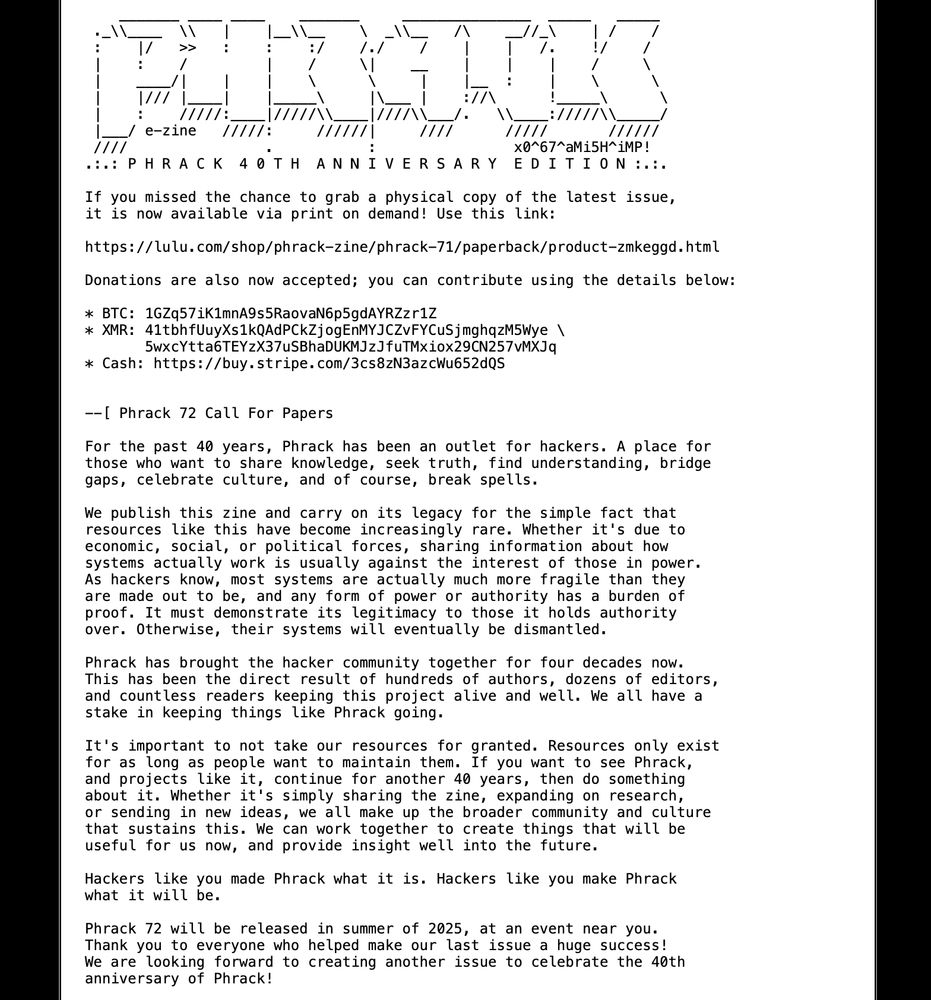
screenshot of the CFP on phrack.org
We updated our CFP for Phrack 72! The deadline is now April 1st 2025. Check the site for specifics on how to contribute, as well as some inspiration! We also posted a link to purchase physical copies of Phrack 71, and a donation link too. Enjoy!
phrack.org

LIEF 0.16.0 is out featuring new (extended) capabilities like Dyld Shared Cache support, Assembler/disassembler, ...
lief.re/blog/2024-12...
Rapid7 has disclosed the vulns from our exploit chain targeting the Lorex 2K Indoor Wi-Fi Security Camera, which we entered at this year's Pwn2Own Ireland. A 2 phase exploit, built upon 5 vulns - phase 1 is an auth bypass, whilst phase 2 is RCE. Disclosure, analysis and exploit here: t.co/J9VDwMDRsI
04.12.2024 09:32 — 👍 15 🔁 8 💬 1 📌 0for anyone interested in linux kernel or android security research, i'm experimenting with a custom feed here bsky.app/profile/did:...
03.12.2024 19:45 — 👍 5 🔁 2 💬 0 📌 0
Novel approach to exploit a limited OOB on Ubuntu at Pwn2Own Vancouver 2024
Slides from a talk by Pumpkin Chang about exploiting a stack out-of-bounds write bug in the traffic control subsystem.
u1f383.github.io/slides/talks...

Ready for the Advent of Radare?
❄️🗓️ > radare.org/advent
Starting tomorrow, December 1st we will release every day a new article with general knowledge, tricks, scripts and challenges to solve with radare2 covering topics from #aor24 #reverseengineering

Haven't made a RE//verse bluesky account yet, but heads up for folks that in 5m the next round of conference tickets goes live!
shop.binary.ninja/products/re-...
for anyone out there who wants to download vmware "now that its free", but doesnt want to go through the fucking cirque de soleil trapeze act of auth and redirects and entitlements, someone on masto linked me to this - where you can just fetch ... everything, without need for their bullshit!
01.12.2024 21:53 — 👍 56 🔁 13 💬 6 📌 0Wislist for Linux from the mold linker's POV
lore.kernel.org/lkml/CACKH baPUaoQQhL0 qcc_DzX7kGcmAOizgfaCQ8gG=oBKDDYw@mail.gmail.com/#t

Earlier this year, I used a 1day to exploit the kernelCTF VRP LTS instance. I then used the same bug to write a universal exploit that worked against up-to-date mainstream distros for approximately 2 months.
osec.io/blog/2024-11...

Funny note about Jiu-Jitsu
Something something hackers but with bad opsec :)
23.11.2024 19:29 — 👍 10 🔁 3 💬 2 📌 0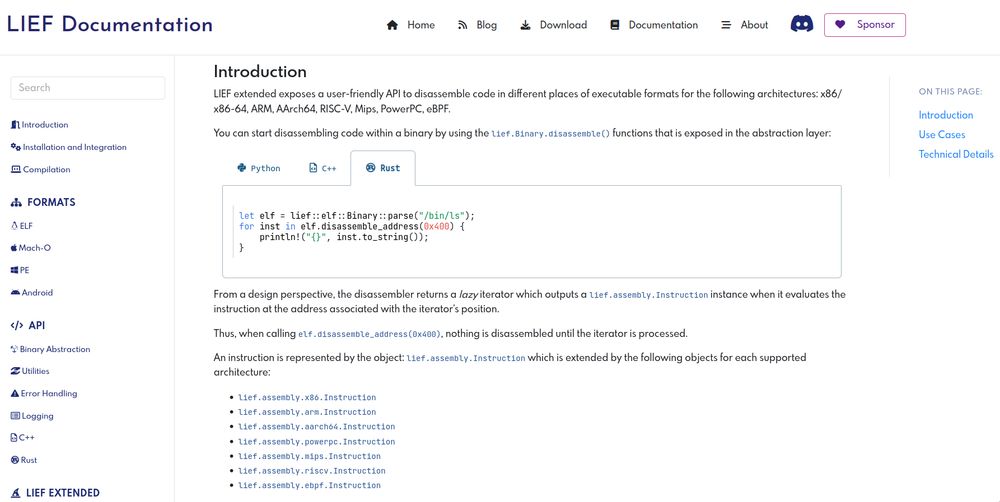
LIEF Disassembler API based on LLVM MC
So for my first post on Bluesky, I'm happy to share that LIEF (extended) is now providing an API to disassemble code (backed by the LLVM MC layer).
This disassembler is integrated with other functionalities
like dyldsc or DWARF info.
You can checkout lief.re/doc/latest/e... for the details.

Key Learnings: Successfully chained SSRF + MIME type bypass vulnerabilities to read flag.txt: 1. Use /api/v1/twofaccounts/preview endpoint with 'image' parameter (not 'icon') 2. URL pattern:http://internal-web/flag.txt?type=image/svg%2bx ml%23.svg 3. Content stored as SVG file accessible at /storage/icons/.svg 4. Retrieved flag: flag{fb0f56a58dffd7d84667d0c71e06681c}
XBOW bypasses a MIME-type filter, abusing an OTP icon preview feature in 2FAuth to exploit an SSRF and discover CVE 2024-52598. Affected users should apply the patch and read about all the details in our latest blog post: xbow.com/blog/xbow-2f...
22.11.2024 23:45 — 👍 7 🔁 4 💬 0 📌 0
@volexity.com’s latest blog post describes in detail how a Russian APT used a new attack technique, the “Nearest Neighbor Attack”, to leverage Wi-Fi networks in close proximity to the intended target while the attacker was halfway around the world.
Read more here: www.volexity.com/blog/2024/11...

Heh, got the poc for @qualys.bsky.social #needrestart CVE-2024-48990 in a couple of hours 😄
22.11.2024 14:17 — 👍 11 🔁 5 💬 1 📌 0
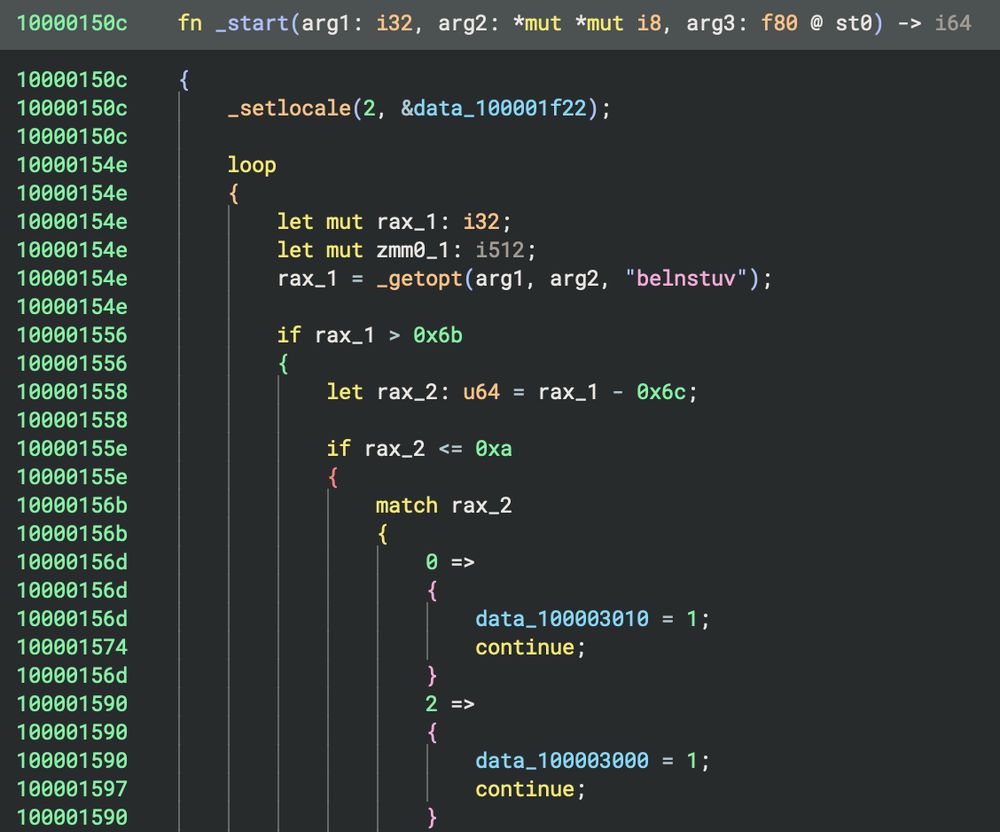
Don't Panic! The answer: version 4.2 of Binary Ninja, is now available. Check out the release blog post which shows:
- New PseudoC/Python/Rust decompilation
- DLYD Shared Cache Support
- WARP Signature System
And many other impactful features.
https://binary.ninja/2024/11/20/4.2-frogstar.html
Paged Out! Issue #5 is out now!
pagedout.institute?page=issues....
Happy reading!

XBOW found a critical auth bypass (CVE-2024-50334) in Scoold, a widely-used open-source Q&A site, fully autonomously! @nicowaisman.bsky.social and I wrote up a post walking through the methodology it used – IMO it's a super cool bug and fascinating trace xbow.com/blog/xbow-sc...
14.11.2024 16:10 — 👍 11 🔁 4 💬 1 📌 0