
🚨Active Exploitation Alert: Critical Apache Tomcat RCE (CVE-2025-24813). Majority of traffic targeting U.S.-based systems. Full analysis & attacker IPs⬇️
#ApacheTomcat #Apache #GreyNoise #Vulnerability #CVE202524813

🚨Active Exploitation Alert: Critical Apache Tomcat RCE (CVE-2025-24813). Majority of traffic targeting U.S.-based systems. Full analysis & attacker IPs⬇️
#ApacheTomcat #Apache #GreyNoise #Vulnerability #CVE202524813

Trump administration does not believe Russia represents a cyber threat against US national security or critical infrastructure? www.theguardian.com/us-news/2025...
28.02.2025 20:34 — 👍 36 🔁 17 💬 2 📌 5
How long can a vulnerable server stay clean on the internet? A honeypot tale. #malware #miner #redtail
🔗 securite360.net/how-long-can...

#BREAKING Europe's security is at a 'turning point': EU chief
17.02.2025 13:02 — 👍 44 🔁 15 💬 3 📌 2
A lire absolument, pour ceux qui souhaitent comprendre l'ampleur de ce que les #databrokers obtiennent comme info sur les internautes.
#adint #cybercriminalité #sensibilisation
Merci #LeMonde pour cet excellent article.
www.lemonde.fr/pixels/artic...

The blog feels like a retro FLARE blog from the good old FireEye days!
Shout out to Nino Isakovic, @qutluch.bsky.social and @lukejenx.bsky.social
cloud.google.com/blog/topics/...
Deobfuscation of Lumma Stealer
ryan-weil.github.io/posts/LUMMA-...
#malware #infosec #stealer #writeup
ReversingLabs researchers have identified 18 malicious VSCode extensions available through the official VSCode Marketplace.
As soon as the extensions were removed from the VSCode Marketplace, the attacker uploaded similar malicious projects on the npm portal.
www.reversinglabs.com/blog/a-new-p...

Spotting PLA activity is rare - every opportunity to investigate matters. Dive in #Nomadpanda #RedFoxtrot #Quickheal #malware securite360.net/a-painful-qu...
13.12.2024 21:08 — 👍 2 🔁 3 💬 0 📌 0
In relation to the RDP phish campaign detailed below: Not sure it's been mentioned, but apparently both the Swedish and Norwegian governments were at least on the target list, judging by these phish domains.
regeringskansliet-se[.]cloud
dep-no[.]cloud
#infosec #apt
microsoft.com/en-us/security/b…

An investigation into Stark Industries reveals it is being used as a global proxy network that conceals the true source of cyberattacks and disinformation campaigns against enemies of Russia.
krebsonsecurity.com/2024/05/star...

Why is a Chinese ship suspect in the damage to Baltic Sea cables? @lemonde.fr has reconstructed the itinerary of the Yi Peng 3, revealing that this merchant ship, now idle between Sweden and Denmark, was precisely sailing above the cables at the time they broke—sometimes down to the exact second.
22.11.2024 09:26 — 👍 20 🔁 4 💬 1 📌 0
Russian spies—likely Russia's GRU intelligence agency—used a new trick to hack a victim in Washington, DC: They remotely infected another network in a building across the street, hijacked a laptop there, then breached the target organization via its Wifi. www.wired.com/story/russia...
22.11.2024 12:06 — 👍 580 🔁 328 💬 12 📌 46
If you're part of civil society and received an Apple notification. The Amnesty Security Lab would be happy to test your phone!
The Apple notification looks like this: support.apple.com/en-us/102174
The Security Lab can be contacted here: securitylab.amnesty.org/get-help/

An Infostealer Searching for « BIP-0039 » Data isc.sans.edu/diary/31464
22.11.2024 04:02 — 👍 6 🔁 3 💬 0 📌 0
Podcast: risky.biz/RBNEWS364/
Newsletter: news.risky.biz/risky-biz-ne...
-US charges five Scattered Spider members
-Apple fixes macOS zero-days
-T-Mobile finally stops a breach
-US takes down PopeyeTools carding portal
-Thailand throws out NSO lawsuit
-Microsoft develops something dumb, part 9,136

A few months' old post but maybe still relevant securite360.net/unveiling-sh...
17.11.2024 14:18 — 👍 1 🔁 0 💬 0 📌 0
Une grenouille et ses têtards
Pour nos prochaines rencontres cyber, nous sommes à la recherche de doctorants volontaires pour parler de leurs travaux (cybersecurité ou manipulation de l'information/réseaux sociaux)
Rejoignez nous pour les "têtards" !
contact@m82-project.org
[CTI insights]
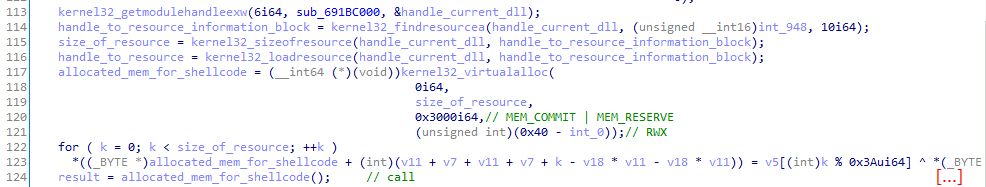
The latest Qakbot payload distributed happened to be packed by the Dave crypter. The DLL decrypts a resource containing Dave's encrypted shellcode and executes it! (cf. securityintelligence.com/x-force/tric...)
Happy to share our new CTI report about Lumma stealer 🕵♂️
18.10.2023 08:46 — 👍 1 🔁 0 💬 0 📌 0
Last friday, we published a report on GuLoader targeting the energy sector in 🇫🇷 and elsewhere.
This report, initially drafted in July for our client, has been recently updated to include new victims we identified.
www.intrinsec.com/wp-content/u...

New #Bumblebee campaign leveraging CVE-2023-38831
Botnet ID : is0210
RC4 key : NEW_BLACK
C2 : g7qf7ew5c[.]life
TTPs : .RAR -> .EXE