Next time you start something and don't finish it, you're behaving quantum!
17.02.2026 21:15 — 👍 9 🔁 1 💬 1 📌 0Next time you start something and don't finish it, you're behaving quantum!
17.02.2026 21:15 — 👍 9 🔁 1 💬 1 📌 0Quantum teleportation, explained by the person who helped invent it. Bill Wootters spoke to us at @perimeterinstitute.ca
17.02.2026 20:46 — 👍 21 🔁 3 💬 0 📌 2
This week I'm in a superposition of writing my PhD thesis and attending QIP 2026 in Riga... ⚛️
26.01.2026 21:58 — 👍 7 🔁 0 💬 0 📌 0
Bless your soul! #QIP2026
26.01.2026 07:25 — 👍 11 🔁 1 💬 0 📌 0
Presented my recent paper “Predicting Module-Lattice Reduction” with Léo Ducas and Paola de Perthuis at Asiacrypt 2025 in Melbourne. A great way to wrap up the year! Merry Chrissy everyone :)
24.12.2025 01:27 — 👍 5 🔁 1 💬 0 📌 0
Abstract. The assumed hardness of the Shortest Vector Problem in high-dimensional lattices is one of the cornerstones of post-quantum cryptography. The fastest known heuristic attacks on SVP are via so-called sieving methods. While these still take exponential time in the dimension d, they are significantly faster than non-heuristic approaches and their heuristic assumptions are verified by extensive experiments. k-Tuple sieving is an iterative method where each iteration takes as input a large number of lattice vectors of a certain norm, and produces an equal number of lattice vectors of slightly smaller norm, by taking sums and differences of k of the input vectors. Iterating these ‘’sieving steps” sufficiently many times produces a short lattice vector. The fastest attacks (both classical and quantum) are for k = 2, but taking larger k reduces the amount of memory required for the attack. In this paper we improve the quantum time complexity of 3-tuple sieving from 2^(0.3098d) to 2^(0.2846d), using a two-level amplitude amplification aided by a preprocessing step that associates the given lattice vectors with nearby’’center points” to focus the search on the neighborhoods of these center points. Our algorithm uses 2^(0.1887d) classical bits and QCRAM bits, and 2^(o(d)) qubits. This is the fastest known quantum algorithm for SVP when total memory is limited to 2^(0.1887d).

Image showing part 2 of abstract.
An Improved Quantum Algorithm for 3-Tuple Lattice Sieving (Lynn Engelberts, Yanlin Chen, Amin Shiraz Gilani, Maya-Iggy van Hoof, Stacey Jeffery, Ronald de Wolf) ia.cr/2025/2189
04.12.2025 16:16 — 👍 2 🔁 2 💬 0 📌 0
Excited to share our new paper on module-lattice reduction! 📄
We analyze the average-case behavior of module-BKZ, identifying when structure offers an advantage over standard BKZ and when the benefits are less clear. We also highlight several open directions for future work.

"Peter Shor states the obvious that there are no existing examples of quantum algorithms available on any quantum hardware that currently show quantum supremacy..."
www.linkedin.com/posts/victor...

The summary slide of Stacey's talk, explaining the differences between algorithms composition in the classical randomized and the quantum worlds, with links to surveys and papers.
From Stacey Jeffery's excellent plenary talk at #TQC2025, on "Composing #Quantum Algorithms"
16.09.2025 05:08 — 👍 19 🔁 2 💬 0 📌 0
My graduating class, 10 years after finishing high school, standing by a tree we once gifted to the school, now replanted.
High school reunion, 10 years later. Great to catch up with old classmates and friends!
07.07.2025 20:28 — 👍 3 🔁 0 💬 0 📌 0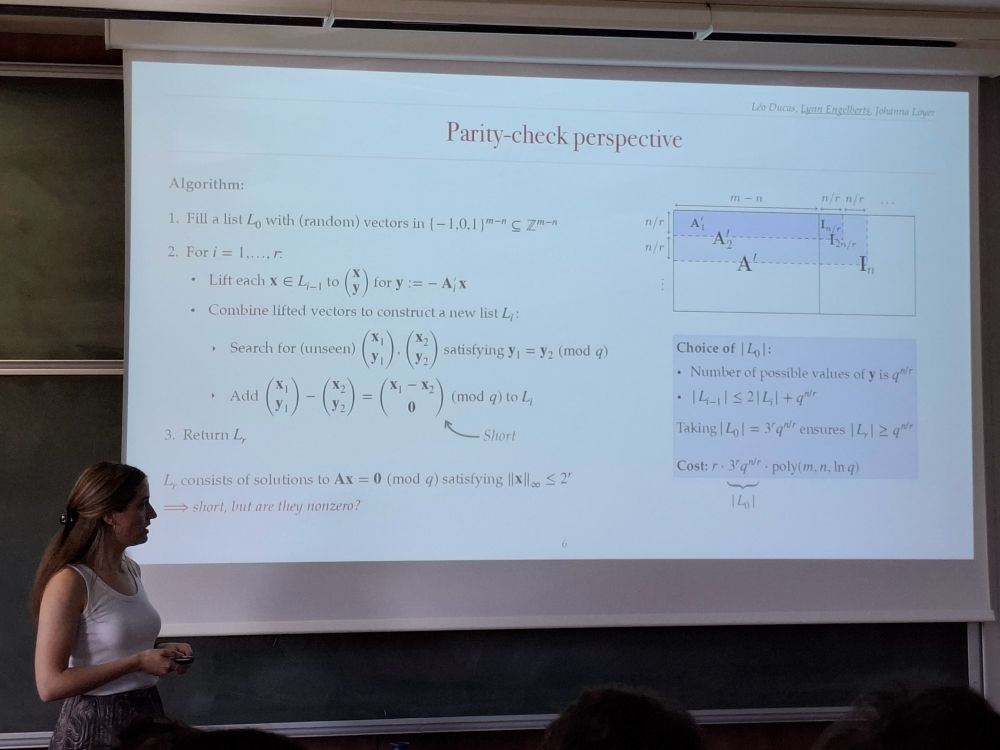
Me presenting our recent work to the other workshop participants in Bordeaux
Had an incredible time in Bordeaux last week at a workshop on algebraic lattices in cryptography! 💎
Huge thanks to Alice Pellet-Mary for organizing and giving me the opportunity to present our recent SIS^∞ paper (eprint.iacr.org/2025/575), to appear in CRYPTO 2025!

A chart for quantum computers, of number of qubits versus error rate, on a logarithmic scale. Broadly it shows a large gap between current quantum computers in the bottom left, and a curve in the top right of the resources they need to break RSA.
An out-of-schedule update to my quantum landscape chart: sam-jaques.appspot.com/quantum_land..., prompted by
@craiggidney.bsky.social 's new paper: arxiv.org/abs/2505.15917.
A startling jump (20x) in how easy quantum factoring can be!
Also: much improved web design!
Thanks @qctip2025.bsky.social for this inspiring conference! Great talks, great people, great vibes.
25.04.2025 15:00 — 👍 2 🔁 0 💬 1 📌 0Excited to join Bluesky! I’m a PhD candidate at CWI and QuSoft, working on quantum & classical algorithms for post-quantum cryptanalysis 🔑. Check out our recent paper here: arxiv.org/abs/2503.23238. Looking forward to connecting with others in quantum computing, cryptography, and beyond!
01.04.2025 19:22 — 👍 10 🔁 2 💬 0 📌 0