
Team member @sigabrt9 was able to bypass Apache FOP Postscript escaping to reach GhostScript engine.
offsec.almond.consulting/bypassing-ap...

Team member @sigabrt9 was able to bypass Apache FOP Postscript escaping to reach GhostScript engine.
offsec.almond.consulting/bypassing-ap...

Team member @myst404 identified a privilege escalation in WAPT caused by a DLL hijacking issue, which was promptly fixed by the vendor. Patched in version 2.6.1.
Changelog: www.wapt.fr/fr/doc/wapt-...

4 channels @ 800 MS/s for < 80€ ? 🥰
TPM sniffing is cheaper than ever
www.cnx-software.com/2025/11/12/6...

Callstacks are largely used by the Elastic EDR to detect malicious activity. SAERXCIT details a technique to evade a callstack-based detection and allow shellcode to load a network module without getting detected.
Post: offsec.almond.consulting/evading-elas...
PoC: github.com/AlmondOffSec...

The proxy view for PipeTap, a Windows Named Pipe Analysis Tool
I've been hacking on a new Windows Named Pipe tool called PipeTap which helps analyse named pipe communications. Born out of necessity while doing some vulnerability research on a target, its been super useful in reversing it's fairly complex protocol. :)
10.09.2025 13:41 — 👍 9 🔁 7 💬 2 📌 3
badsuccessordumper.py is not dead!*
gist.github.com/ThePirateWho...
*terms and conditions apply


🫡 @synacktiv.com
22.08.2025 13:14 — 👍 0 🔁 0 💬 0 📌 0
The code is here. As always, "Not tested in prod, use at your own risk".
All credit goes to YuG0rd, snovvcrash and fulc2um.
gist.github.com/ThePirateWho...

dMSA are now supported by impacket (thanks fulc2um!), so its time for `badsuccessordumper.py` !
github.com/fortra/impac...

Following ShitSecure's TROOPERS talk and release of BitlockMove, we're releasing our internal DCOMRunAs PoC made by SAERXCIT last year.
It uses a similar technique with a few differences, such as DLL hijacking to avoid registry modification.
github.com/AlmondOffSec...

TIL there is a pure Powershell port of PassTheCert, by TheViperOne. Kudos 🫡
github.com/The-Viper-On...

Deleting a file in Wire doesn’t remove it from servers — and other findings
Did you know deleting a file in Wire doesn’t remove it from servers?
Team member myst404 took a closer look at Wire's asset handling and identified 5 cases where behaviors may diverge from user expectations.
offsec.almond.consulting/deleting-fil...

Elitebook x360 1040 G10: you can sniff the TPM via flash 25Q256JVEN (chip U367). CLK is 25Mhz.
21.06.2025 12:25 — 👍 0 🔁 0 💬 0 📌 0
1k stars 🌟 Thank you everyone
12.06.2025 09:11 — 👍 1 🔁 0 💬 0 📌 0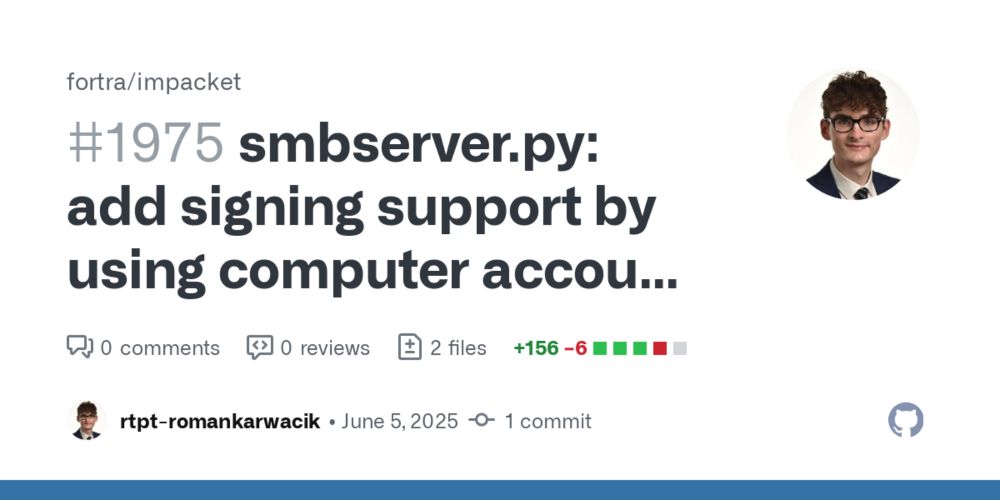
Newer Windows clients often enforce signing ✍️ when using SMB fileshares.
To quickly deploy an SMB server with signing supported we implemented this in impacket's smbserver.py based on a prior work by @lowercasedrm.bsky.social .
github.com/fortra/impac...

ldap3 is not dead! 🥳 🎉
github.com/cannatag/lda...
If someone stumbles upon this:
➡️ Lenovo T470: SOIC8 clip U49 chip (CLK 15Mhz)
➡️ Elitebook 1040G3: SOIC8 clip U23 chip (CLK 33Mhz)


Recently sniff a SPI bus for the first time (with and without PIN) on a Lenovo T470. It's quite fun, event with a DSLogic! s/o @en4rab.bsky.social for SPITkey.
17.04.2025 06:59 — 👍 2 🔁 1 💬 1 📌 0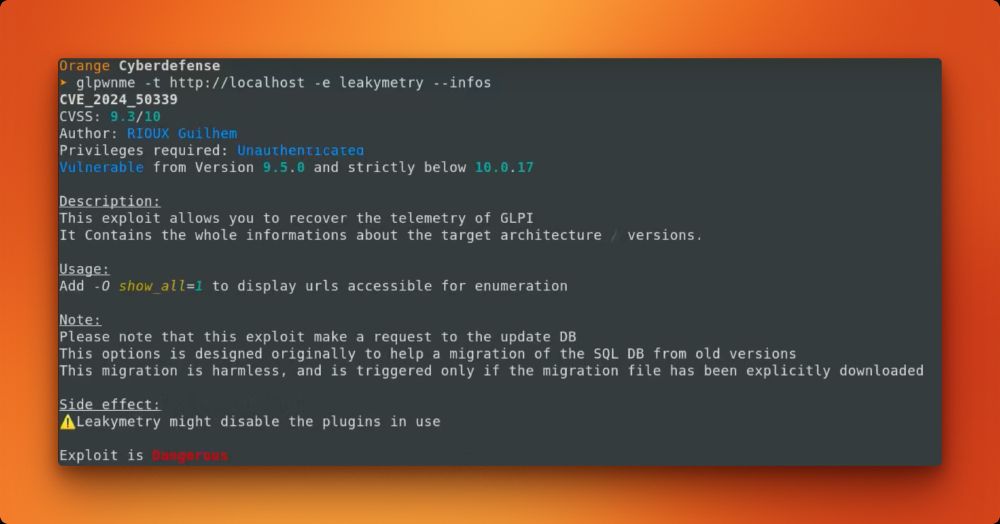
Screenshot from the YouTube POC showing output from the tool highlighting that an instance is vulnerable › glpwnme -t http://localhost -e leakymetry --infos CVE_2024_50339 CVSS: 9.3/10 Author: RIOUX Guilhem Privileges required: Unauthenticated Vulnerable from Version 9.5.0 and strictly below 10.0.17 Description: This exploit allows you to recover the telemetry of GLPI. It Contains the whole informations about the target architecture / versions. Usage: Add -0 show_all=1 to display urls accessible for enumeration Please note that this exploit make a request to the update DB This options is designed originally to help a migration of the SQL DB from old versions This migration is harmless, and is triggered only if the migration file has been explicitly downloaded Side effect: Leakymetry might disable the plugins in use Exploit is Dangerous Orange Cyberdefense
GLPI (popular in France & Brazil) versions 9.5.0-10.0.16 allow hijacking sessions of authenticated users remotely. The details & process of discovering the vulnerability is detailed by @GuilhemRioux here:
sensepost.com/blog/2025/le...
Tooling: github.com/Orange-Cyber...
Demo: youtu.be/OTaCV4-6qHE

#pywerview 0.7.3 is out!
github.com/the-useless-...
🌻


Another free #impacket IoC: just search for packets with Auth Context ID = 79231 within your DCERPC traffic.🕵️♂️
08.03.2025 22:29 — 👍 0 🔁 0 💬 0 📌 0
A screenshot that shows a python script window and a wireshark window
i was bored at night, so i played with the netsync attack.
Meet netdumper.py, a pure TCP RPC based script to netsync machine (and gMSA!) accounts. Nothing new, mostly based on previous works by @exploitph @4ndr3w6S, @evi1cg et al.
gist.github.com/ThePirateWho...
🌻

PR has been merged into #impacket 🥳
19.02.2025 08:45 — 👍 1 🔁 0 💬 0 📌 0
Netlogon used as SSP (AES version) to perform lsaLookupSid3.
gist.github.com/ThePirateWho...
All you need is #impacket PR 1848