Under India’s pressure, Facebook let propaganda and hate speech thrive
Facebook has retreated from its professed ideals in India under pressure from Prime Minister Narendra Modi’s Bharatiya Janata Party.
Here we go. Free, no-reg versions of favorite stories from my four years at the Washington Post. First, three pieces from our Pulitzer-finalist series on how India's ruling party coerced U.S. tech giants into violating their own policies. www.washingtonpost.com/world/2023/0...
24.02.2026 22:23 —
👍 135
🔁 60
💬 2
📌 6
YouTube video by SentinelOne
LABScon25 Replay | Hacktivism and War: A Clarifying Discussion | Jim Walter
Hacktivism and War -- always worth listening to Jim 👇
www.youtube.com/watch?v=sNaO...
10.02.2026 15:15 —
👍 1
🔁 0
💬 0
📌 0
LABScon 2025
🔥 The lineup this year is incredible, thanks to everyone who submitted!
Attendees are in for something special… and for everyone else, expect some major FOMO.
events.sentinelone.com/event/LABSco...
05.09.2025 17:57 —
👍 2
🔁 2
💬 0
📌 0
LABScon 2025
🔥 The lineup this year is incredible, thanks to everyone who submitted!
Attendees are in for something special… and for everyone else, expect some major FOMO.
events.sentinelone.com/event/LABSco...
05.09.2025 17:57 —
👍 2
🔁 2
💬 0
📌 0
Contagious Interview | North Korean Threat Actors Reveal Plans and Ops by Abusing Cyber Intel Platforms
DPRK-aligned threat actors abuse CTI platforms to detect infrastructure exposure and scout for new assets.
New research from @milenkowski.bsky.social (S1) and @kennethkinion.bsky.social (Validin):
🇰🇵 Contagious Interview | North Korean Threat Actors Reveal Plans and Ops by Abusing Cyber Intel Platforms
Research: www.sentinelone.com/labs/contagi...
Reuters story: www.reuters.com/world/asia-p...
04.09.2025 14:45 —
👍 7
🔁 5
💬 0
📌 0
The US, AU, and NZ have tested a prototype for a new cyber defense kit designed to connect and help secure any network.
The kits are operated by a nine-person team and are intended to be portable and moved to any location in the world.
www.defence.gov.au/news-events/...
02.09.2025 14:57 —
👍 4
🔁 4
💬 1
📌 1
🔥 The hunt is on for the world’s ultimate threat hunter? 🔍
🛡️Introducing Sentinels League: The Threat Hunting World Championships 🛡️ 3 Rounds. 3 Regions. 3 Finalists. Only One World Champion.
26.08.2025 19:16 —
👍 5
🔁 3
💬 2
📌 0
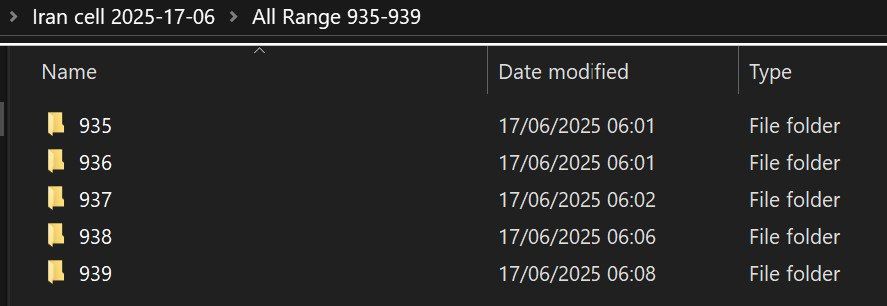
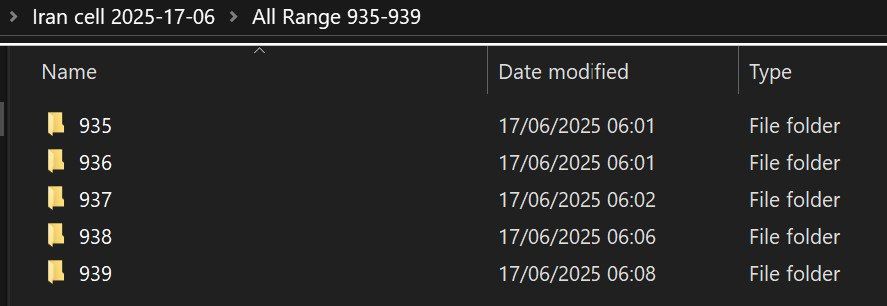
Screenshot from Predatory Swallow's Telegram channel, showing folders purporting to hold IranCell data
Someone claiming to be Gonjeshke Darande (Predatory Sparrow) has posted ~2GB of what *appears to be* IranCell subscriber data, covering the 935-939 prefixes.
#privacy #breach #mobile #iran
17.06.2025 15:54 —
👍 4
🔁 1
💬 0
📌 0

Hefty new drop w/ @milenkowski.bsky.social
China-nexus Threat Actors Hammer At the Doors of Top Tier Targets
www.sentinelone.com/labs/follow-...
09.06.2025 16:42 —
👍 7
🔁 3
💬 0
📌 0

Dutch intelligence discover a new Russian APT—LAUNDRY BEAR
www.aivd.nl/documenten/p...
Microsoft calls it Void Blizzard. Their report is here: www.microsoft.com/en-us/securi...
27.05.2025 12:11 —
👍 21
🔁 12
💬 1
📌 1

Is the era of the “named actor” done?
As the OG adversary sets diverge, get promoted, or move on
actors dispersing across the kill chain based on specialized skills increases (ORBs, criminal underground)
AND the CTI models maturing…
APTs ⬇️⬇️
UNCs ⬆️⬆️
21.05.2025 20:15 —
👍 28
🔁 8
💬 7
📌 0

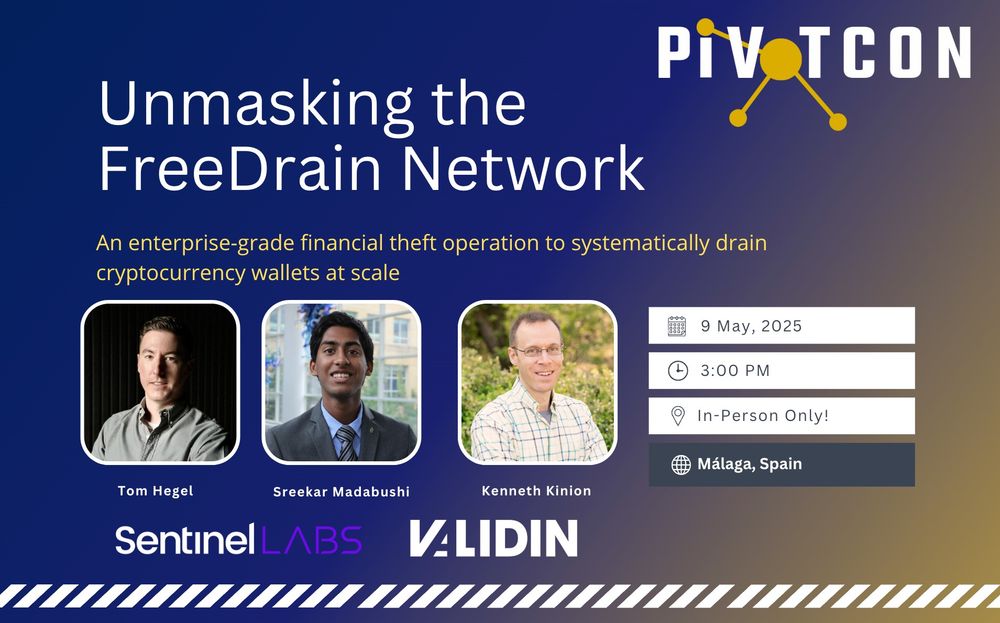
NEW 👉 FreeDrain Unmasked | Uncovering an Industrial-Scale Crypto Theft Network
Months-long research project with Validin we just dropped @pivotcon.bsky.social
🖤~40k IOCs: github.com/Validin/indi...
💜 SentinelLabs: s1.ai/freedrain
💙 Validin: www.validin.com/blog/freedra...
Enjoy!
08.05.2025 15:39 —
👍 9
🔁 5
💬 0
📌 0

NEW 👉 FreeDrain Unmasked | Uncovering an Industrial-Scale Crypto Theft Network
Months-long research project with Validin we just dropped @pivotcon.bsky.social
🖤~40k IOCs: github.com/Validin/indi...
💜 SentinelLabs: s1.ai/freedrain
💙 Validin: www.validin.com/blog/freedra...
Enjoy!
08.05.2025 15:39 —
👍 9
🔁 5
💬 0
📌 0

Top Tier Target | What It Takes to Defend a Cybersecurity Company from Today's Adversaries
This report highlights a rarely-discussed but crucially important attack surface: security vendors themselves.
An absolutely stunning look inside @sentinelone.com 's use of #synapse to provide intelligence context to inter-disciplinary intelligence stakeholders in defense of their own org. Truly on the leading edge of the intel driven fusion, collaboration, and impact. 🤩
www.sentinelone.com/labs/top-tie...
28.04.2025 23:36 —
👍 24
🔁 10
💬 1
📌 0

At @pivotcon.bsky.social, I'm presenting with @hegel.bsky.social and Sreekar Madabushi on the first public look at the full scope of a stealthy, long-running phishing network.
24.04.2025 14:31 —
👍 7
🔁 5
💬 0
📌 0

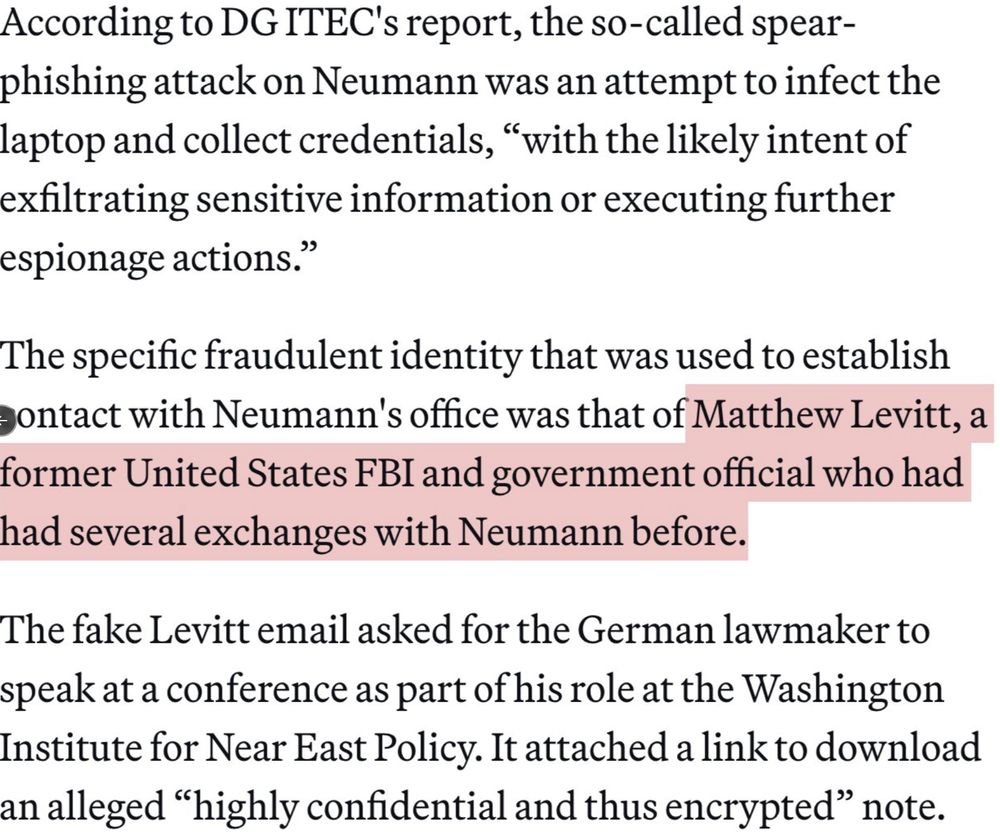
Text from https://www.politico.eu/article/european-parliament-iran-delegation-chair-victim-tehran-linked-hacking-hannah-neumann/

Text from https://www.politico.eu/article/european-parliament-iran-delegation-chair-victim-tehran-linked-hacking-hannah-neumann/
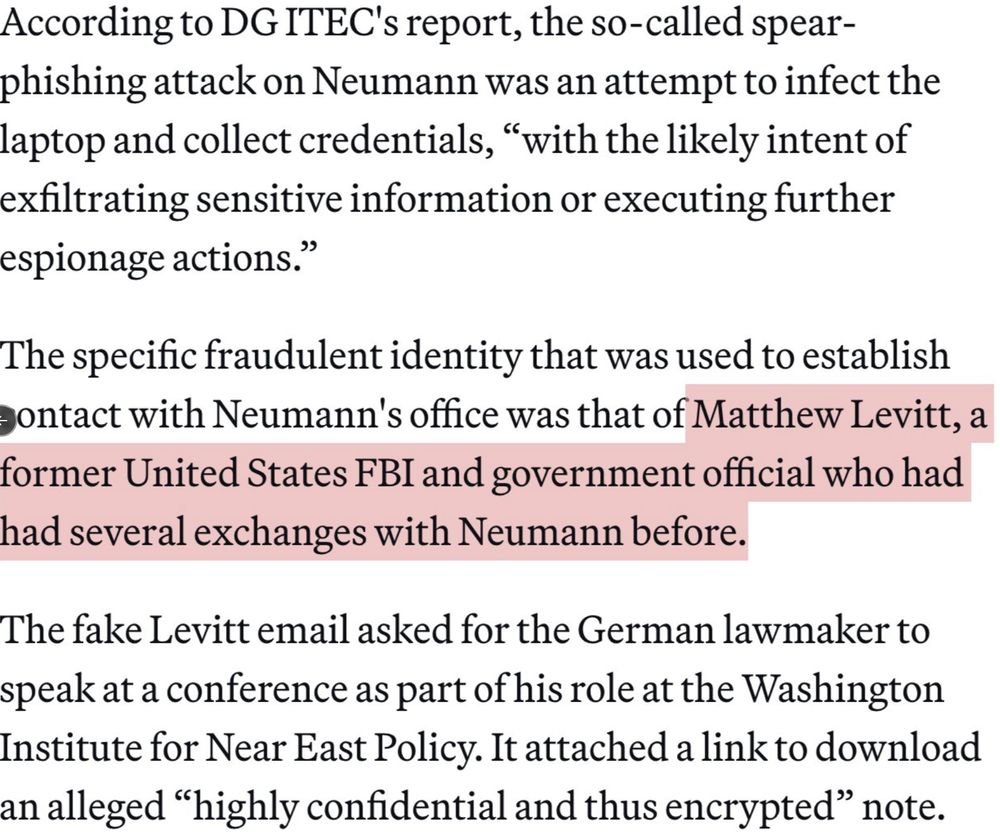
Text from https://www.politico.eu/article/european-parliament-iran-delegation-chair-victim-tehran-linked-hacking-hannah-neumann/
NEW: Iranian gov hackers targeted #EU Parliament's #Iran delegation chair @hneumannmep.bsky.social
Elaborate operation impersonated former #FBI official to seed spyware.
Good to see a MEP speaking out & sharing this insidious threat to EU institutions 1/
www.politico.eu/article/euro...
23.04.2025 20:49 —
👍 43
🔁 23
💬 1
📌 1
#apt #sidewinder "54th CISM World Military Naval Pentathlon Championship 2025.docx"
40712a087a8280425f1b317e34e265c0329ffb0057be298d519fc5e0af6cb58f
-> dirsports.milqq[.]info
blank doc decoy
11.04.2025 14:25 —
👍 2
🔁 3
💬 0
📌 0
Not Reality: Exploring Meta-themed Phishing with Validin | Validin
Not Reality: Exploring Meta-themed Phishing with Validin
@bushidotoken.net explored a Meta-themed credential phishing campaign (not "Reality"). From those indicators, I pulled the "Threads" & this is far from an isolated campaign. Found great pivots in registration "Meta"data. (I'll see myself out.)
All 762 indicators 💥⤵️
www.validin.com/blog/not_rea...
07.04.2025 14:49 —
👍 2
🔁 2
💬 0
📌 0
Here's the Lab Dookhtegan segment
www.youtube.com/watch?v=g-zj...
01.04.2025 17:47 —
👍 4
🔁 1
💬 0
📌 0
Really great episode this week. The Signal ID management mess, and the lab dookhtegan topics.. simply delicious 🤌
30.03.2025 21:10 —
👍 9
🔁 2
💬 0
📌 1

Pulling the Threads on the Phish of Troy Hunt | Validin
Connecting a successful phishing attempt to Scattered Spider through Validin pivoting
Atomic indicators have value beyond just the day they’re observed - Age alone doesn’t always diminish their usefulness.
Attribution challenges aside, this is a common occurrence in both cybercrime and APT campaigns. Looking at you, South Asia!
28.03.2025 17:20 —
👍 2
🔁 0
💬 0
📌 0
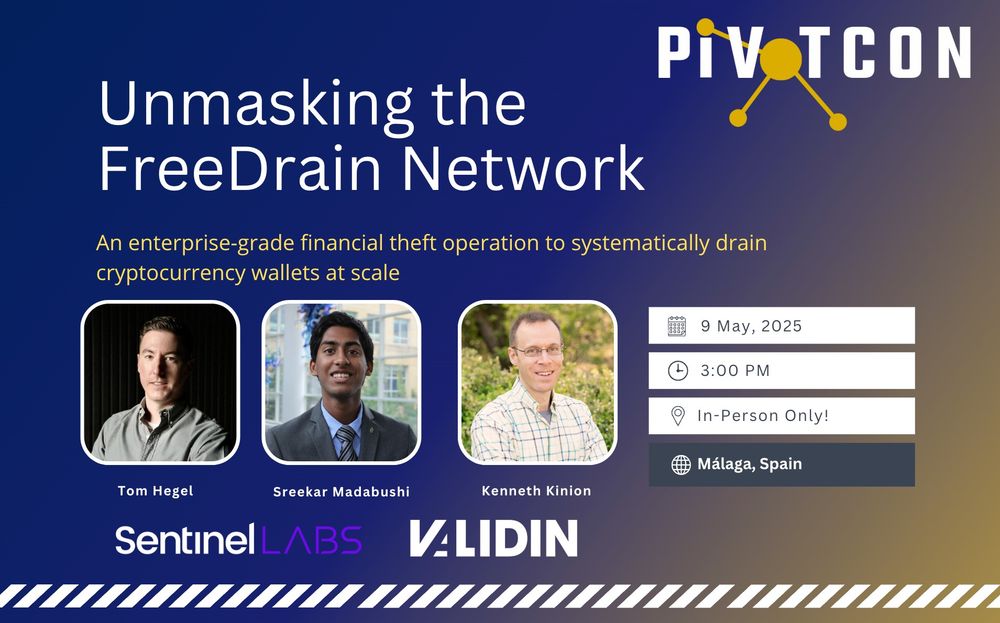
Incredibly excited to drop some new research alongside @kennethkinion.bsky.social and Sreekar Madabushi at this years @pivotcon.bsky.social
10.03.2025 13:59 —
👍 7
🔁 1
💬 0
📌 0
Great refresher / inside-scoop on the Lamberts -- #WhereAreTheyNow
08.03.2025 22:19 —
👍 1
🔁 1
💬 0
📌 0

#dprk #apt 2024년 귀속 연말정산 안내문_세한.docx.lnk
b81513f0f8d3db382bb8f931bf2b7a0d4f26f74cfcf60b5d889de87ef2f1d543 -> www.roofcolor[.]com/wp-includes/js/src/list.php , www.acschoolcatering[.]com/libraries/src/inc/ decoy:
28.02.2025 15:29 —
👍 1
🔁 1
💬 0
📌 0
Look man, I'm not saying anything but I'm also not NOT saying anything
23.02.2025 01:43 —
👍 21
🔁 5
💬 2
📌 0