PingOne Attack Paths - SpecterOps
You can use PingOneHound in conjunction with BloodHound Community Edition to discover, analyze, execute, and remediate identity-based attack paths in PingOne instances.
Introducing PingOneHound! This OpenGraph extension for BloodHound can help you identify, analyze, execute, and remediate attack paths in PingOne organizations. Read the introductory blog post here: specterops.io/blog/2025/10...
20.10.2025 17:43 —
👍 9
🔁 10
💬 0
📌 0

Dough No! Revisiting Cookie Theft - SpecterOps
Explore how cookie theft has evolved in Chromium browsers with the shift from DPAPI to App-Bound encryption. This post breaks down modern cookie stealing techniques via COM, remote debugging, and exte...
Cookie theft has evolved. 🍪
Over the last year, stealing cookies on Windows devices has changed significantly for Chromium browsers like Chrome and Edge. Andrew Gomez dives into these changes, how threat actors adapt, & new detection opportunities. ghst.ly/45S1ZgW
27.08.2025 16:55 —
👍 5
🔁 2
💬 0
📌 0
Check out my new blog on nested app authentication.
13.08.2025 16:43 —
👍 6
🔁 5
💬 0
📌 0

If you use CIS Benchmarks, I highly advise against this recommendation...
This disables cloud delivered protection which underpins a bunch of capabilities, disables roughly half of your protection
Fortunately, if you enable Tamper Protection, it is forcefully enabled for you :)
01.08.2025 20:12 —
👍 20
🔁 2
💬 2
📌 1
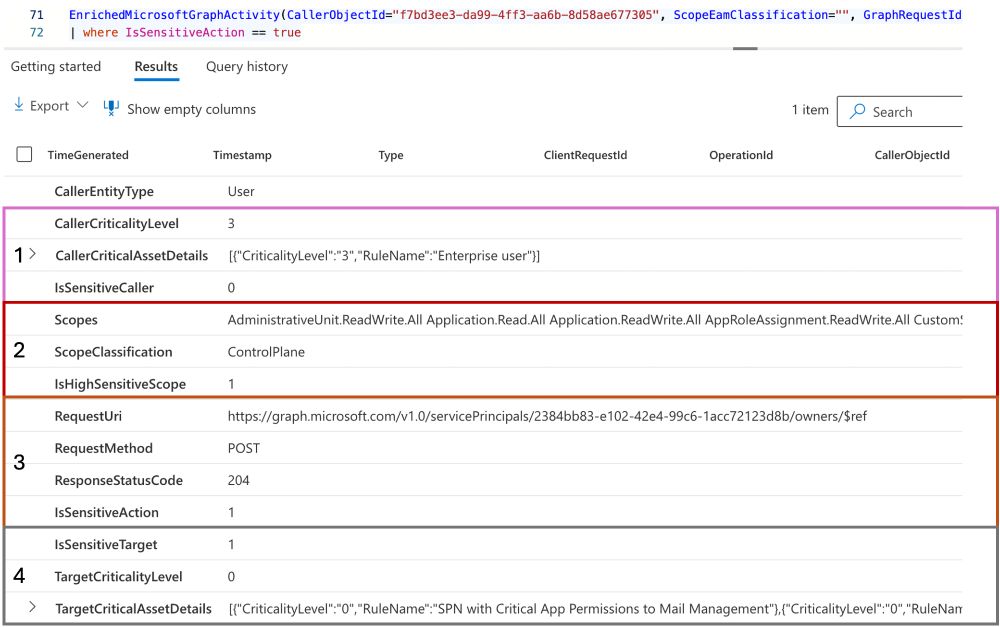
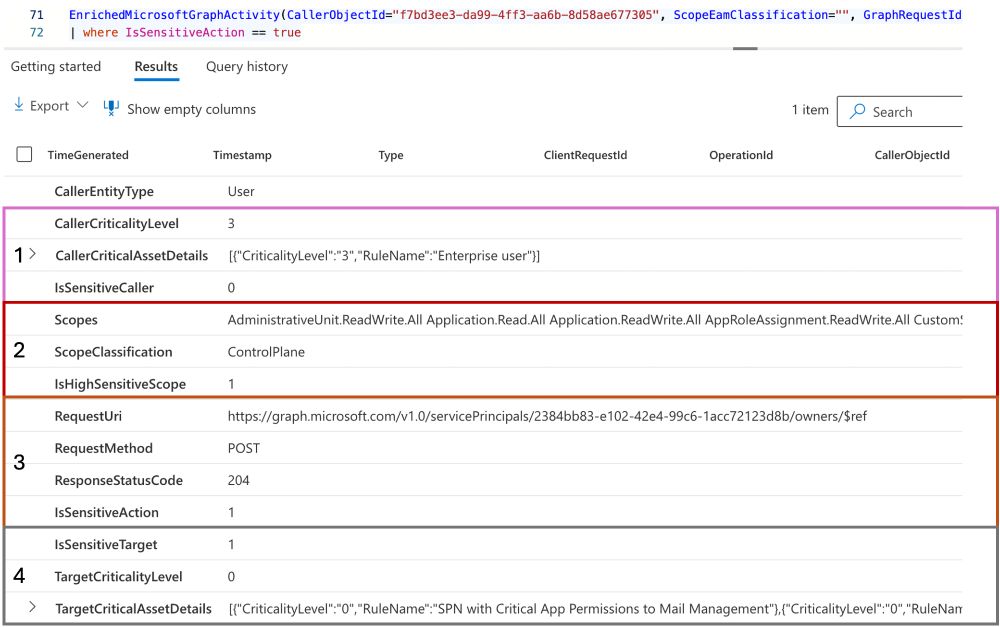
🚀🔎 Track Sensitive Graph API Calls with my new #KQL Function for #MicrosoftDefenderXDR
Microsoft has released the new advanced hunting table "GraphAPIAuditEvents" which offers great opportunities to investigate activities based on #MicrosoftGraph API calls.
17.07.2025 06:43 —
👍 3
🔁 2
💬 1
📌 0

Machine Learning Series Chapter 1 - SpecterOps
This article explores core machine learning concepts through Micrograd, a minimal autograd engine. It covers regression, classification, loss functions, gradients, and backpropagation with examples. W...
Dive into the world of machine learning! ⚙️
Kicking off his blog series, Diego Lomellini uses Micrograd to explain core ML concepts like supervised learning, regression, classification, loss functions, & gradient descent. ghst.ly/44n3IeJ
02.07.2025 18:06 —
👍 1
🔁 1
💬 0
📌 0
Actually, it's very helpful to trigger a LPE on servers by placing the missing wlanapi.dll in a writable %path% location by a non-admin user ;)
28.06.2025 11:31 —
👍 1
🔁 0
💬 0
📌 0
GitHub - SpecterOps/Nemesis: An offensive data enrichment pipeline
An offensive data enrichment pipeline. Contribute to SpecterOps/Nemesis development by creating an account on GitHub.
Happy Friday! @tifkin.bsky.social and I are happy to announce that we have cut the release for Nemesis 2.0.0 - check out the CHANGELOG for a (brief) summary of changes, and dive into our new docs for more detail! We're extremely proud and excited for this release github.com/SpecterOps/N...
28.06.2025 04:14 —
👍 12
🔁 6
💬 0
📌 0

Misconfiguration Manager: Still Overlooked, Still Overprivileged - SpecterOps
It has been one year since Misconfiguration Manager's release and SCCM misconfigurations remain widespread, leading to dangerous attack paths across enterprises. Here we summarize the impact and commu...
In the year since Misconfiguration Manager's release, the security community has been actively researching new tradecraft & identifying new attack paths.
@subat0mik.bsky.social & @unsignedsh0rt.bsky.social dive into the research & its impact on the state of SCCM security. Read more: ghst.ly/460vI9d
26.06.2025 15:52 —
👍 3
🔁 3
💬 0
📌 0
Presentations and external blogs
Dirk-jan’s personal blog, mostly containing research on topics I find interesting, such as (Azure) Active Directory internals, protocols and vulnerabilities.
Last two weeks I talked about BYO Identity Providers in Entra ID and backdoors to External Auth Methods to bypass MFA. Only possible because MSFT doesn't implement the mandatory OIDC security measures. Slides with optional dark mode on: dirkjanm.io/talks/
24.06.2025 07:12 —
👍 11
🔁 5
💬 1
📌 1

Administrator Protection Review - SpecterOps
Microsoft will be introducing Administrator Protection into Windows 11. This post explores security considerations for red teamers.
Get the scoop on the incoming Administrator Protection for Windows 11.
@xpnsec.com covers the architecture, access controls, and why some legacy UAC bypass techniques remain effective in his latest blog post. ghst.ly/44mw5JM
18.06.2025 18:34 —
👍 5
🔁 2
💬 0
📌 1
We are VERY excited to announce that Volatility 3 has now reached feature parity with Volatility 2! With this parity release, Volatility 2 is now deprecated. Full details in the blog post linked below.
16.05.2025 15:08 —
👍 20
🔁 11
💬 0
📌 0

The SQL Server Crypto Detour - SpecterOps
As part of my role as Service Architect here at SpecterOps, one of the things I’m tasked with is exploring all kinds of technologies to help those on assessments with advancing their engagement. Not l...
Celebrating 1 year at SpecterOps, this was the first project I worked on after starting. Looking at SQL Server Transparent Data Encryption, how to bruteforce weak keys, and how ManageEngine's ADSelfService product uses TDE with a suspect key. Enjoy :) specterops.io/blog/2025/04...
08.04.2025 16:03 —
👍 15
🔁 3
💬 1
📌 0
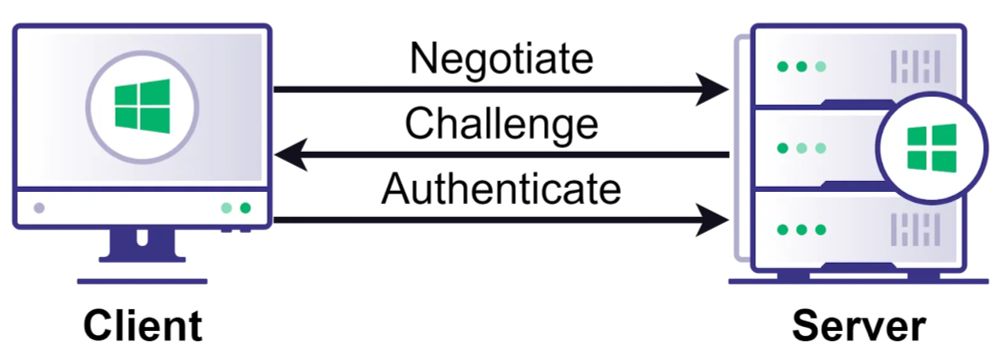
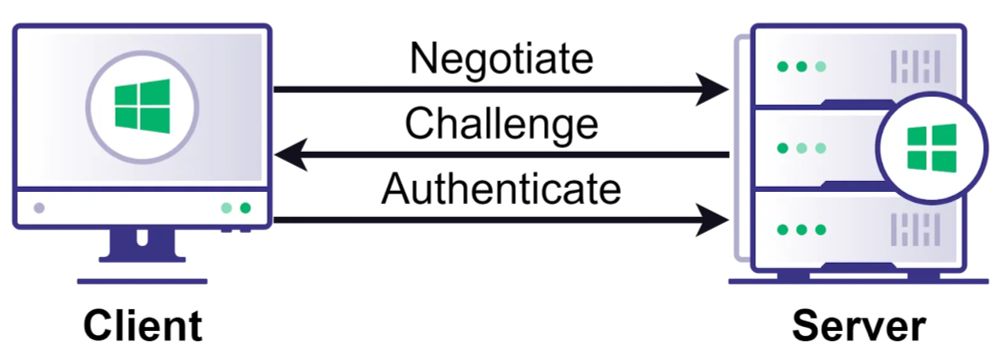
Think NTLM relay is a solved problem? Think again.
Relay attacks are more complicated than many people realize. Check out this deep dive from Elad Shamir on NTLM relay attacks & the new edges we recently added to BloodHound. ghst.ly/4lv3E31
08.04.2025 23:00 —
👍 27
🔁 20
💬 1
📌 2
GitHub - decoder-it/KrbRelayEx-RPC
Contribute to decoder-it/KrbRelayEx-RPC development by creating an account on GitHub.
KrbRelayEx-RPC tool is out! 🎉
Intercepts ISystemActivator requests, extracts Kerberos AP-REQ & dynamic port bindings and relays the AP-REQ to access SMB shares or HTTP ADCS, all fully transparent to the victim ;)
github.com/decoder-it/K...
14.03.2025 10:18 —
👍 9
🔁 10
💬 0
📌 0
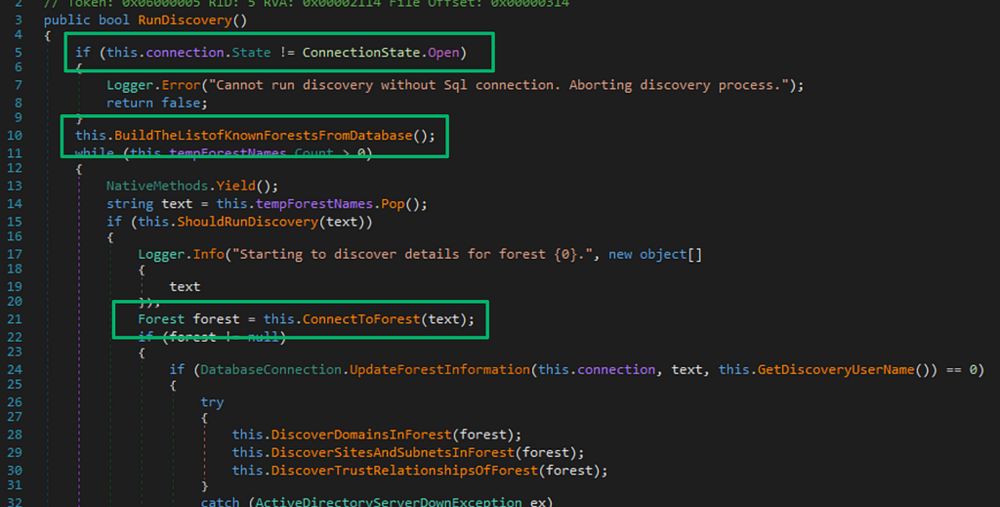
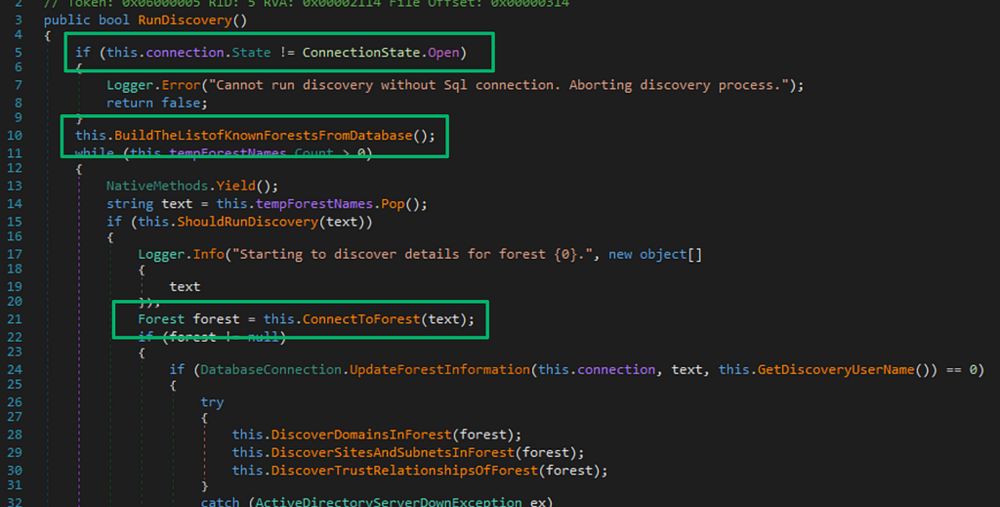
Decrypting the Forest From the Trees - SpecterOps
TL;DR: SCCM forest discovery accounts can be decrypted including accounts used for managing untrusted forests. If the site server is a managed client, service account credentials can be decrypted via ...
#SCCM forest discovery accounts can be decrypted—even those for untrusted forests. If the site server is a managed client, all creds can be decrypted via Administration Service API.
Check out our latest blog post from @unsignedsh0rt.bsky.social to learn more. ghst.ly/4buoISp
06.03.2025 20:34 —
👍 22
🔁 15
💬 1
📌 0
Normally you can't auth to Entra ID connected webapps with bearer tokens. But if Teams can open SharePoint/OneDrive with an access token, I guess so can we. roadtx now supports opening SharePoint with access tokens in the embedded browser 😀
18.02.2025 13:12 —
👍 19
🔁 8
💬 1
📌 0
ROADtools update: I just released roadlib v1.0! This version drops the adal dependency, all auth flows are now implemented natively 🎉 This was mostly a personal goal, but it helps with adding new features, such as forcing MFA during device code auth independent of CA policies 😀
07.02.2025 14:50 —
👍 31
🔁 11
💬 2
📌 0
Abusing multicast poisoning for pre-authenticated Kerberos relay over HTTP with Responder and krbrelayx
In our latest article, @croco_byte proposes an implementation of a trick discovered by James Forshaw in his research regarding Kerberos relaying. Discover how to perform pre-authenticated Kerberos relay over HTTP with our Responder and krbrelayx pull requests!
www.synacktiv.com/publications...
27.01.2025 12:06 —
👍 16
🔁 12
💬 0
📌 1