Top 10 web hacking techniques of 2025
Welcome to the community vote for the Top 10 Web Hacking Techniques of 2025.
Honored to be nominated for the @portswigger.net Top 10 Web Hacking Techniques 2025 with my research "Playing with HTTP/2 CONNECT".
Make sure to check out the full list and cast your vote!
portswigger.net/polls/top-10...
19.01.2026 11:34 —
👍 0
🔁 0
💬 0
📌 0
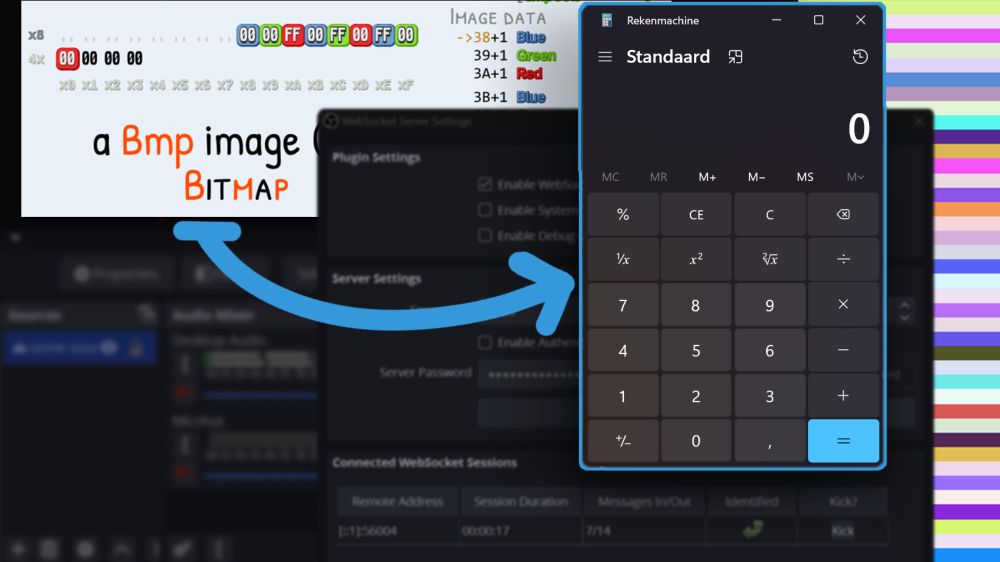
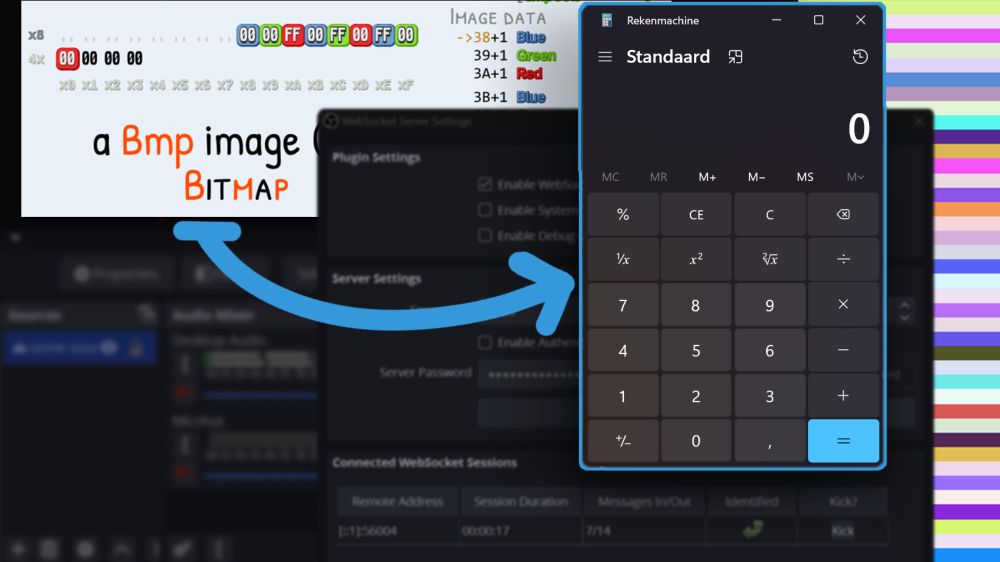
OBS WebSocket to RCE | Jorian Woltjer
Disabling password authentication of your OBS WebSocket server can have devastating consequences. We'll attack from the browser to construct an RCE payload on Windows formed from the pixels of an imag...
Just pushed a new frontend for my site, and a new post!
This one's about an tricky file write vulnerability on Windows in OBS. By crafting an image with very specific pixels, we can plant a backdoor on your PC all from an attacker's site by misconfiguring:
jorianwoltjer.com/blog/p/resea...
05.06.2025 18:48 —
👍 5
🔁 2
💬 1
📌 0
Walkthrough 2023
Ever wondered how Kurts Maultaschenfabrikle got hacked in 2023? The full story, all technical details, out now ;-) apply-if-you-can.com/walkthrough/...
21.02.2025 10:31 —
👍 7
🔁 10
💬 0
📌 0