
Chinese robot maker Unitree has removed a problematic component from the firmware of its Go1 robot dog that could have allowed remote attackers to take over the robot
www.scmp.com/tech/tech-tr...

Chinese robot maker Unitree has removed a problematic component from the firmware of its Go1 robot dog that could have allowed remote attackers to take over the robot
www.scmp.com/tech/tech-tr...

the takeover has begun..
trainings start tomorrow morning!
Happy to share my slides from BOOTSTRAP25. Unfortunately the bug discussed is still not patched in Linux 6.14.0 despite it being reported explicitly. Slides are in markdown but there's a PDF in "releases" too github.com/jduck/bs25-s...
25.03.2025 19:26 — 👍 14 🔁 7 💬 1 📌 0Delighted that our paper on "Grammar mutation for testing input parsers" - led by Bachir Bendrissou and joint with @ccadar.bsky.social - is now published in ACM TOSEM! This came from a registered report at FUZZING. Check it out! doc.ic.ac.uk/~afd/papers/...
14.01.2025 10:19 — 👍 14 🔁 6 💬 1 📌 0
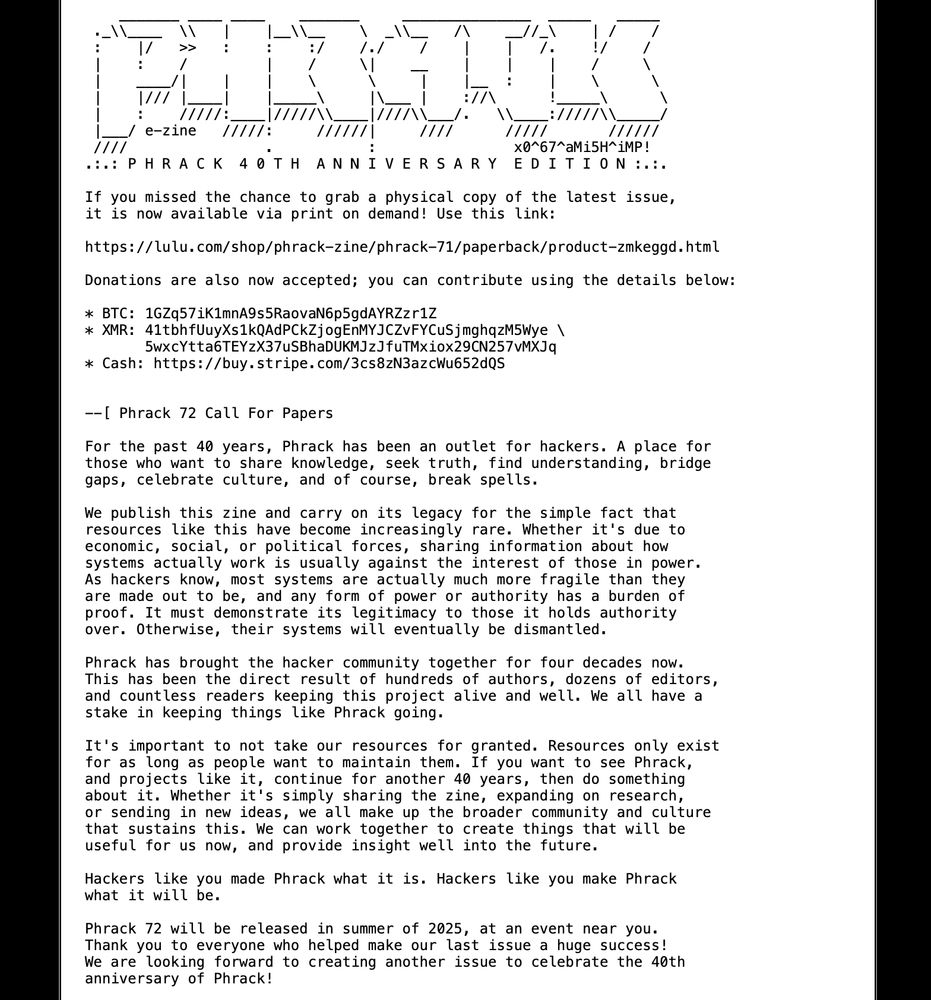
Phrack Graffiti Logo
Reminder that the Phrack 72 CFP closes APRIL 1ST 2025. Get your papers in and come be a part of our fabulous 40th anniversary issue!
See phrack.org for more info
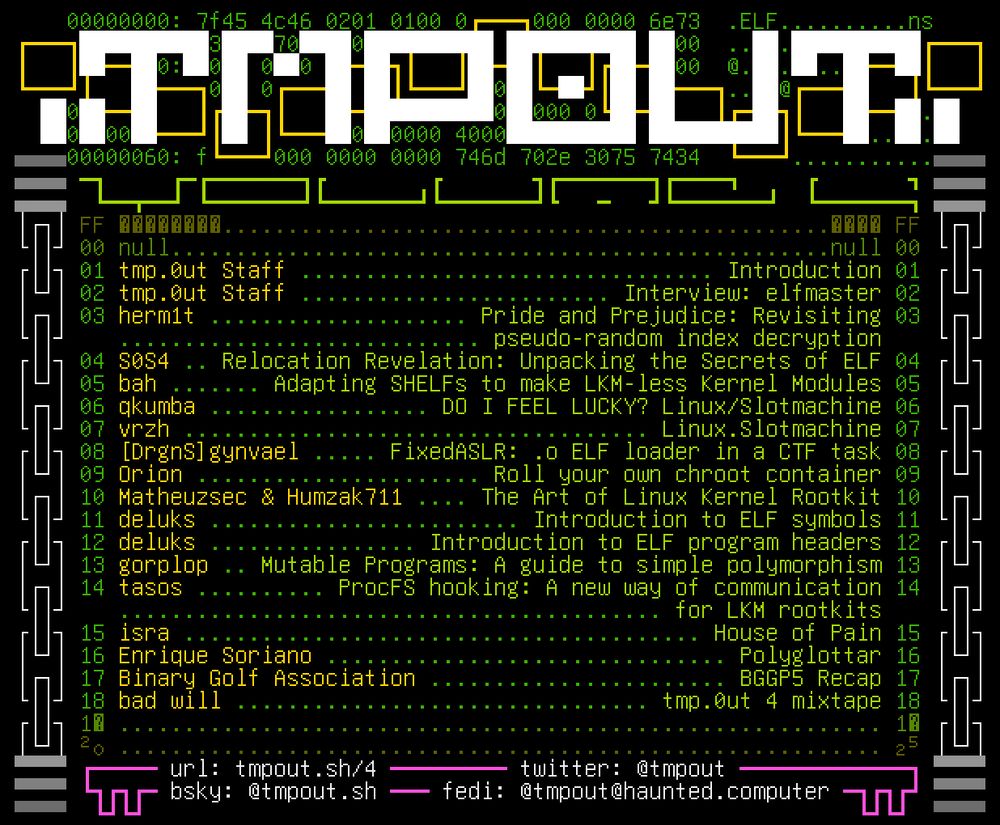
table of contents for tmp.0ut volume 4
Would you look at that, it's tmp.0ut Volume 4! Happy Friday, hope you enjoy this latest issue!
tmpout.sh/4/
Only a week and a half left for USENIX WOOT '25 conference submissions - deadline March 11 AoE. We’re looking forward to seeing even more of your amazing offensive security papers this year! And still a few days for up-and-coming track (March 4). CfP at www.usenix.org/conference/w...
28.02.2025 20:56 — 👍 5 🔁 10 💬 0 📌 2
We discover 119 vulnerabilities in LTE/5G core infrastructure, each of which can result in persistent denial of cell service to an entire metropolitan area or city and some of which can be used to remotely compromise and access the cellular core.
https://cellularsecurity.org/ransacked

I watch and read and I’ve seen a manner research. But this research into visualising Wi-Fi signals using an array of ESP32 chips is something else.
www.youtube.com/watch?v=sXwD...
It is that good. That deep and frankly so out there and he calls himself a mediocre engineer too. WTF?
Blown away.
Hackers rejoice!
We are releasing the Phrack 71 PDF for you today!
Don't forget this year is Phrack's 40th anniversary release! Send in your contribution and be part of this historical issue!
The CFP is still open, you can find it and the PDF link at phrack.org
Update your AMD Zen processor's BIOS: www.amd.com/en/resources...
Check with your OEM for BIOS updates with the new microcode patches, they have had some time to address this high importance item.

2024 was a significant year for decompilation, constituting a possible resurgence in the field. Major talks, the thirty-year anniversary of research, movements in AI, and an all-time high for top publications in decompilation.
Join me for a retrospective:
mahaloz.re/dec-progr...
Just unrestricted an issue that shows a fun new attack surface. Android RCS locally transcribes incoming media, making vulnerabilities audio codecs now fully-remote. This bug in an obscure Samsung S24 codec is 0-click
project-zero.issues.chromium.org/issues/36869...
OMG, Orange Tsai released his latest new research 🤯 💣
blog.orange.tw/posts/2025-0...
Which will you be watching?
26.12.2024 08:11 — 👍 0 🔁 0 💬 0 📌 0
Ten Years of Rowhammer: A Retrospect (and Path to the Future)
fahrplan.events.ccc.de/congress/202...
From Convenience to Contagion: The Libarchive Vulnerabilities Lurking in Windows 11
fahrplan.events.ccc.de/congress/202...

Dialing into the Past: RCE via the Fax Machine – Because Why Not?
fahrplan.events.ccc.de/congress/202...
Beyond BLE: Cracking Open the Black-Box of RF Microcontrollers
fahrplan.events.ccc.de/congress/202...
From Pegasus to Predator - The evolution of Commercial Spyware on iOS
fahrplan.events.ccc.de/congress/202...
Auracast: Breaking Broadcast LE Audio Before It Hits the Shelves
fahrplan.events.ccc.de/congress/202...
From fault injection to RCE: Analyzing a Bluetooth tracker
fahrplan.events.ccc.de/congress/202...
Proprietary silicon ICs and dubious marketing claims? Let's fight those with a microscope!
fahrplan.events.ccc.de/congress/202...
Hacking the RP2350
fahrplan.events.ccc.de/congress/202...
Looking through the schedule of #38c3 which starts tomorrow. Some talks I’ll be watching the streams for this year:
ACE up the sleeve: Hacking into Apple's new USB-C Controller
fahrplan.events.ccc.de/congress/202...
Liberating Wi-Fi on the ESP32
fahrplan.events.ccc.de/congress/202...

vacation reading material acquired!
23.12.2024 15:32 — 👍 5 🔁 0 💬 0 📌 0


Pretty interesting technique used by _mccaulay here to understand the heap better and aid exploitation of a TP-Link vulnerability!
www.nccgroup.com/uk/research-...
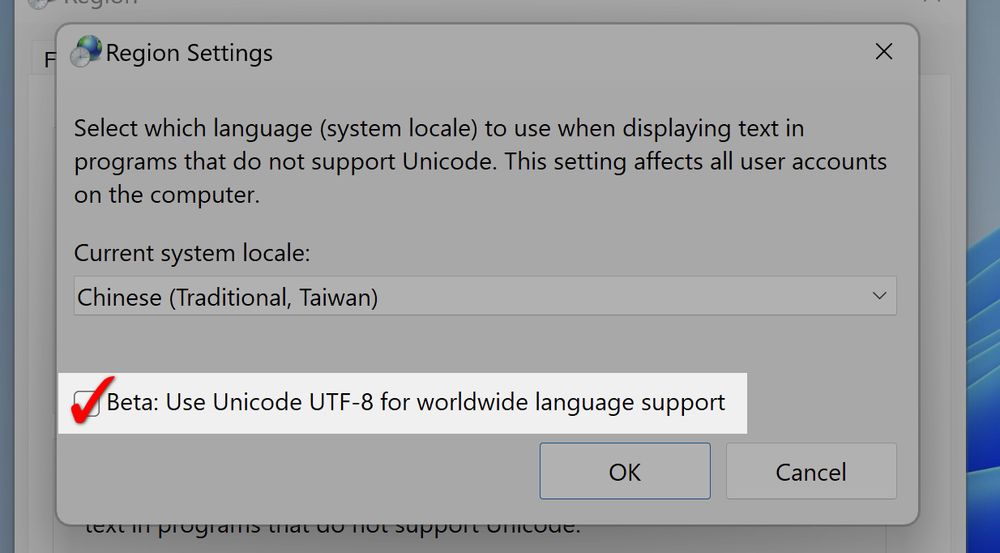
screenshot of the CFP on phrack.org
We updated our CFP for Phrack 72! The deadline is now April 1st 2025. Check the site for specifics on how to contribute, as well as some inspiration! We also posted a link to purchase physical copies of Phrack 71, and a donation link too. Enjoy!
phrack.org
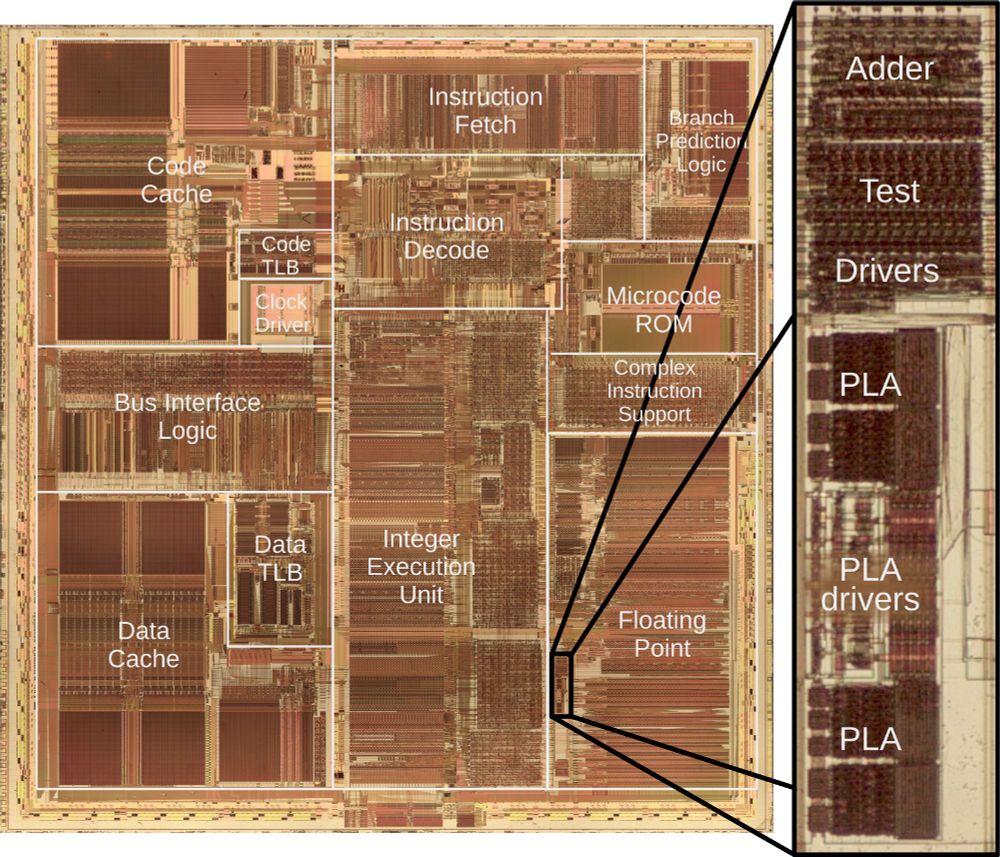
A die photo of the Pentium processor with the main functional blocks labeled including the caches, instruction fetch and decode, integer execution, and floating point. The image consists of complex patterns of rectangular regions in reddish and brownish colors. The image zooms in on a small part of the floating point unit giving a detail of an adder and PLA circuit.
Intel launched the Pentium processor in 1993. Unfortunately, dividing sometimes gave a slightly wrong answer, the famous FDIV bug. Replacing the faulty chips cost Intel $475 million. I reverse-engineered the circuitry and can explain the bug. 1/9
06.12.2024 16:48 — 👍 711 🔁 235 💬 16 📌 27I wrote a fun, little blog post. Remote pre-auth file deletion in SolarWinds ARM allowed to achieve LPE on AD machines 🙃
12.12.2024 18:03 — 👍 9 🔁 6 💬 1 📌 0
A PoC for that Cleo zero-day is now live: labs.watchtowr.com/cleo-cve-202...
12.12.2024 00:04 — 👍 12 🔁 8 💬 0 📌 0
New DCOM lateral movement technique discovered that bypasses traditional defenses. Unlike previous attacks relying on IDispatch interfaces, this method exploits undocumented COM interfaces within MSI, specifically targeting IMsiServer and IMsiCustomAction interfaces. 1/7
12.12.2024 00:00 — 👍 21 🔁 17 💬 2 📌 0
Course materials for Modern Binary Exploitation by RPISEC
github.com/RPISEC/MBE?s... via @alexplaskett.bsky.social
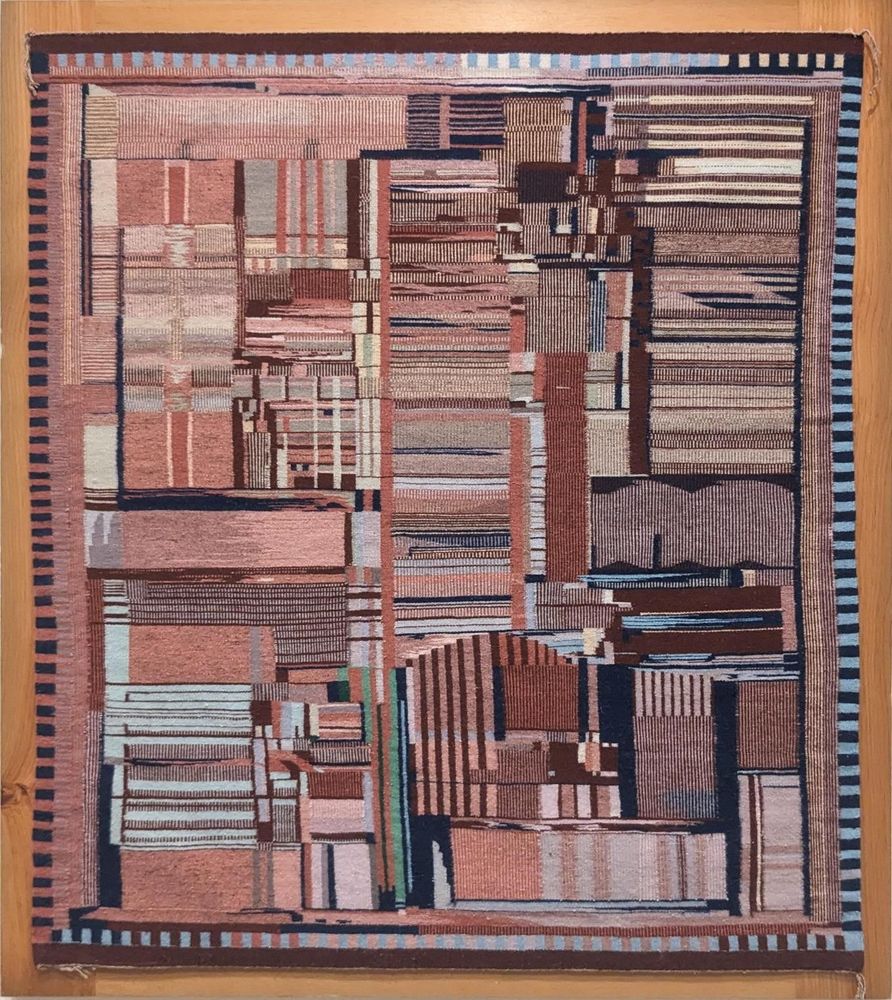
A Navajo rug with a complex pattern with muted reds, pinks and blues. The pattern consists of various vertical and horizontal rectangles with stripes. Around the border are small alternating black and colored rectangles. The weaving is mounted in a wooden frame and hanging on the museum wall.
I recently saw an amazing Navajo rug at the National Gallery of Art. It looks abstract at first, but it is a detailed representation of the Intel Pentium processor. Called "Replica of a Chip", it was created in 1994 by Marilou Schultz, a Navajo/Diné weaver and math teacher. 1/n
25.11.2024 16:29 — 👍 2928 🔁 922 💬 35 📌 69
If you're interested in the technical details, I wrote the blog post here: flatt.tech/research/pos...
For the further details, please check out the announcement from the OpenWrt team: lists.openwrt.org/pipermail/op... (2/2)