
Identity security in restricted environments shouldn’t be limited to periodic reviews.
BloodHound Enterprise on-premises enables continuous Identity Attack Path Management without cloud connectivity.
Learn more ➡️ ghst.ly/4kadAi0

Identity security in restricted environments shouldn’t be limited to periodic reviews.
BloodHound Enterprise on-premises enables continuous Identity Attack Path Management without cloud connectivity.
Learn more ➡️ ghst.ly/4kadAi0

The only conference dedicated to Attack Path Management is back!
3 tracks. Real-world case studies. Hands-on BloodHound Quest lab. Join us at #SOCON2026 and advance your identity-first security strategy.
🎟️ Save 25% with early bird: specterops.io/so-con

We've got a fresh #BloodHoundBasics post from @jonas-bk.bsky.social!
Ever wondered about those obscure AD special identity groups that quietly grant permissions to every principal in your environment?
With BloodHound, you can uncover compromising permissions tied to these groups.
🧵: 1/2

DEF CON releases, PDQ SmartDeploy creds (@unsigned_sh0rt), FortiSIEM root command injection (@SinSinology), a cat themed loader (@vxunderground), fine-tune LLMs for offsec (@kyleavery_), juicing NTDS.DIT (@MGrafnetter), and more!
blog.badsectorlabs.com/last-week-in...
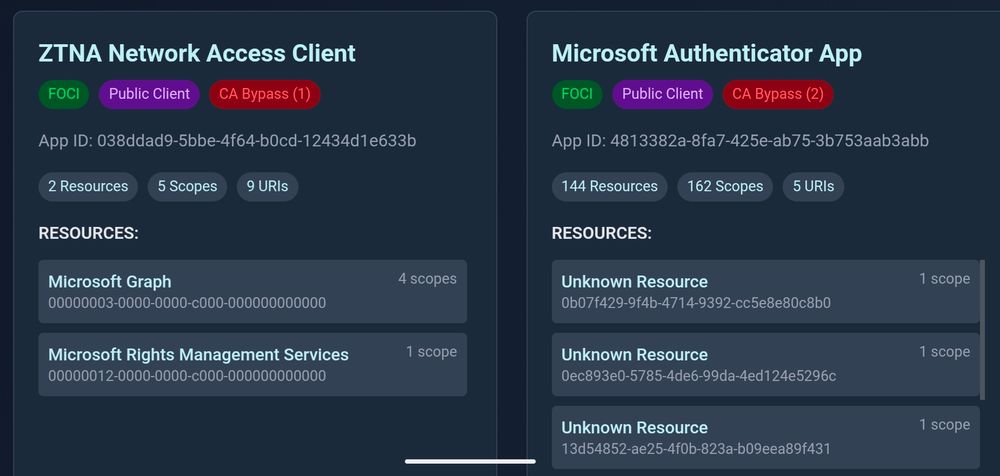
One of the results of the joined research with @dirkjanm.io is entrascopes.com
Basically the yellow pages for Microsoft first party apps.
#TROOPERS25
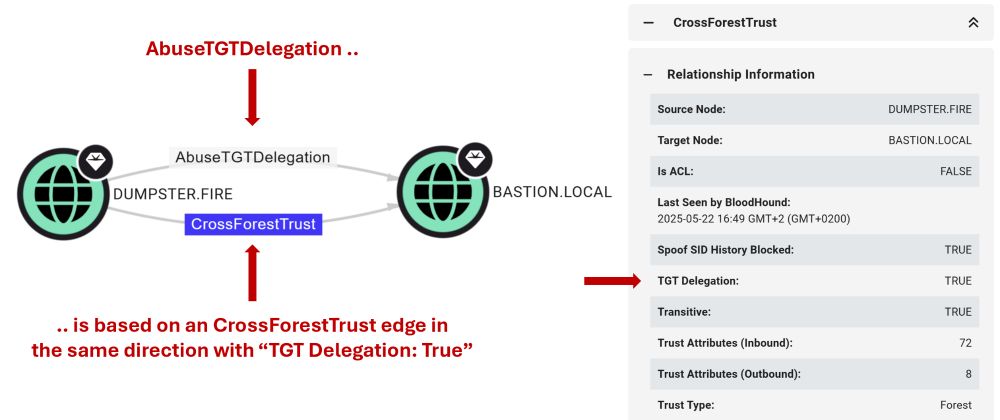
I publish two blog posts today! 📝🐫
First dives into how we're improving the way BloodHound models attack paths through AD trusts: specterops.io/blog/2025/06...
Second covers an attack technique I came across while exploring AD trust abuse: specterops.io/blog/2025/06...
Hope you enjoy the read 🥳

Introducing the BloodHound Query Library! 📚
@martinsohn.dk & @joeydreijer.bsky.social explore the new collection of Cypher queries designed to help BloodHound users to unlock the full potential of the BloodHound platform by creating an open query ecosystem. ghst.ly/4jTgRQQ
Received the news today that my talk "Advanced Active Directory to Entra ID lateral movement techniques" was also accepted for @defcon.bsky.social 🎉 hope to see everyone there!
10.06.2025 12:28 — 👍 27 🔁 5 💬 0 📌 0
New tricks, same impact
posts.specterops.io/update-dumpi...



It's #BloodHoundBasics day! 🙌
The docs got a fresh new look and live at bloodhound.specterops.io — now back in the GitHub repo too, so PRs are welcome!
s/o @jonas-bk.bsky.social
Getting started w/ Mythic? We've got you covered.
@its-a-feature.bsky.social walks through the web UI basics, login process, & how to configure your default username/password. Check it out! ▶️ ghst.ly/user-interface
Watch the full series: ghst.ly/mythic-op
Thrilled to be speaking at @wearetroopers.bsky.social again this year - can’t wait to be back! 🥳
17.04.2025 16:00 — 👍 5 🔁 1 💬 0 📌 0Highly recommend this one. It's a good read :)
09.04.2025 04:27 — 👍 1 🔁 0 💬 0 📌 0
Had a blast at #SOCON2025!
It was great to meet up with colleagues and friends 💜
The slides from my presentation are available here: github.com/JonasBK/Pres...




That's all folks! 👋 Thank you to everyone who attended & presented talks during our #SOCON2025 conference days. Our training courses kickoff tomorrow at 9AM back at Convene.
01.04.2025 23:34 — 👍 4 🔁 2 💬 0 📌 0
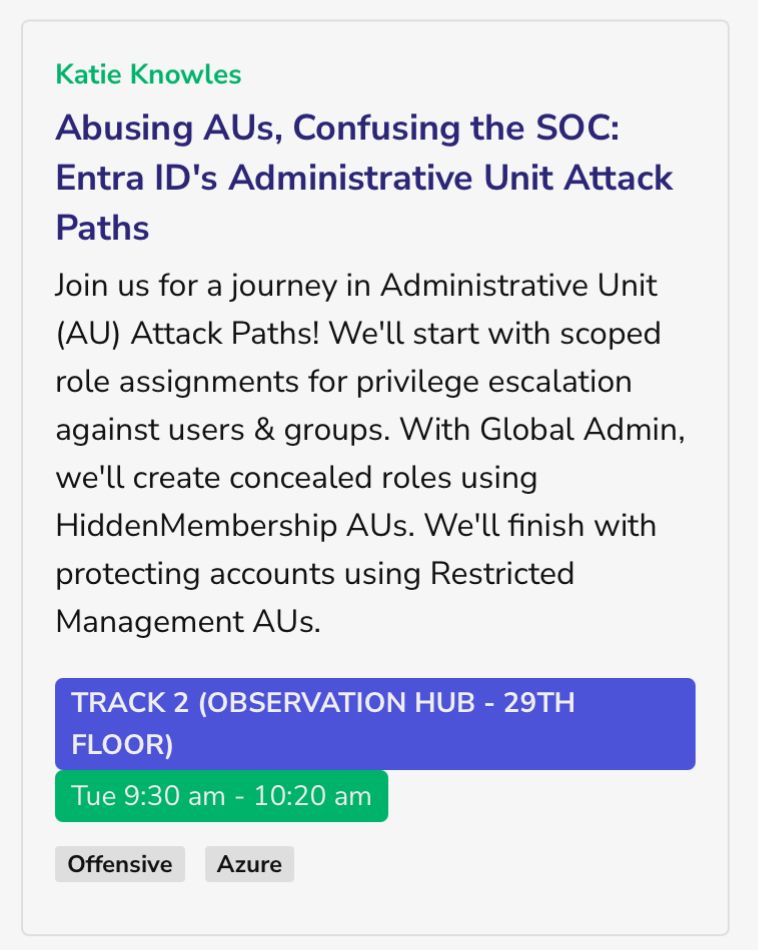
Excited to be at @specterops.bsky.social SO-CON this week!! If you're around, I'll be presenting "Abusing AUs, Confusing the SOC" tomorrow bright & early:
31.03.2025 14:39 — 👍 15 🔁 7 💬 1 📌 0
If you missed the session on NTLM at #SOCON2025, you're in luck! Join @tifkin.bsky.social, @cptjesus.bsky.social, and @harmj0y.bsky.social on April 17 for a webinar discussing their research into modeling NTLM relay attacks within BloodHound.
Register today! ➡️ ghst.ly/ntlm-web




Day 1 at #SOCON2025 has wrapped! 👊
We will see you right back here tomorrow for even more great content from our speakers. Check out the agenda for Day 2 at specterops.io/so-con.

It’s #BloodHoundBasics Day! 🎉
Want to find relationships cross AD domains? Use this Cypher query:
MATCH p = (x:Base)-->(y:Base)
WHERE x.domain <> y.domain
AND NOT COALESCE(x.system_tags, '') CONTAINS 'admin_tier_0'
RETURN p
LIMIT 100
(1/2)

Active Directory isn't going anywhere, but security pros lack key knowledge. 🧠
Join @jimsycurity.adminsdholder.com & Darryl Baker at @bsidescharm.bsky.social for their AD Security 101 training, which aims to give you tools to find & fix misconfigurations attackers exploit. bsidescharm.org
The query excludes Tier Zero control to filter out legit permissions granted to groups such as Enterprise Admins.
The screenshot is redacted, but can you guess the name of the group in the middle? Hint: It has something to do with emails.
s/o @jonas-bk.bsky.social
(2/2)
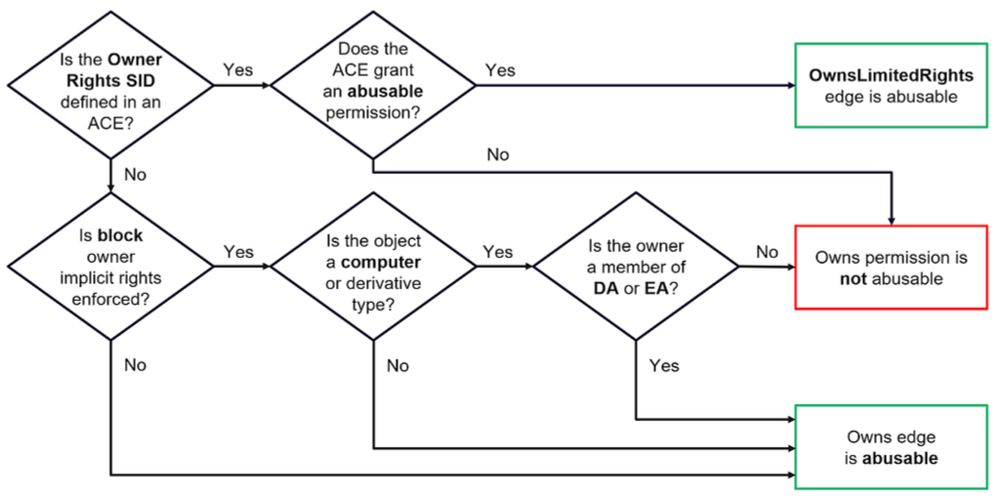
Accurately see what permissions are exploitable in your AD environment. Chris Thompson discusses a recent update in BloodHound that shows fewer false positives for Owns/WriteOwner edges, & introduces the new Owns/WriteOwnerLimitedRights edges.
Read more: ghst.ly/3QORQdF

Next.js auth bypass (@zhero___ + @inzo____), ServiceNow for red teamers (@__invictus_), Veeam RCE - again! (@chudyPB), ArgFuscator (@Wietze), and more!
blog.badsectorlabs.com/last-week-in...

Before locking in for the OSCP exam, it’s highly recommended to complete the practical lab networks. @anam0x.bsky.social shares his tips on how to maximize the lab experience in Part 3 of his blog series: ghst.ly/4iDWjML
🧵: 1/4
What's the purpose of the x-ms-DeviceCredential header if the device id claim is already included in the user access token? It seems redundant
21.03.2025 17:48 — 👍 1 🔁 1 💬 0 📌 0
Happy #BloodHoundBasics day! This week we are looking at how BloodHound classifies Tier Zero.
Q: Why is not just the DA group Tier Zero but also all members?
A: BloodHound classifies a few default Tier Zero assets, then adds more w/ logic from known attack techniques.
1/8

Super excited to be speaking at SO‑CON 2025 on March 31st with my coworker Lance Cain. We’re diving into an example attack path from real-life red team assessments by Lance Cain, Dan Mayer, myself, and the entire @specterops.bsky.social crew. specterops.io/so-con/ #SOCON2025 #redteam
22.03.2025 17:38 — 👍 4 🔁 1 💬 0 📌 0
On PTO and bored, so playing around with MCP by exposing Mythic APIs to Claude and seeing what the result. Attempting to have it emulate threat actors while operating Apollo in a lab... would make a good sparring partner :D www.youtube.com/watch?v=ZooT...
20.03.2025 22:24 — 👍 20 🔁 6 💬 1 📌 0
Part 2 of Nathan Davis' Getting Started with BloodHound Enterprise series just dropped!
Check out the latest post on understanding & contextualizing Tier Zero, & ensuring you have an accurate depiction of the Attack Paths that exist in your BHE tenant. ghst.ly/4kEebbK

Evilginx Pro (@mrgretzky.breakdev.org ), Pre-auth RCE in a CMS (@chudypb.bsky.social), GOAD ADCS, YouTube email disclosure (@brutecat.com), SAML parser bug (ulldma.bsky.social), and more!
blog.badsectorlabs.com/last-week-in...