I am very happy to announce that thanks to the hard work of many people (The "MIKE Team"), we now have a working implementation in SageMath of MIKE (Module Isogeny Key Exchange).
20.02.2026 15:04 — 👍 8 🔁 8 💬 1 📌 3
It depends if you interpret the waiting period to apply to the authors or to the paper :)
I think CiC and CHES have some form of this, but it doesn't automatically apply to all rejections: if the reviewers think the paper needs significantly more work, the authors cannot resubmit immediately
03.02.2026 07:29 — 👍 0 🔁 0 💬 0 📌 0
A waiting period may not be the best option, but we probably need some kind of pre-review check. Right now, it takes very little work for authors to resubmit the same paper again and again until it gets through, while it takes the 3+ reviewers a considerable amount of work to re-review the paper
03.02.2026 07:09 — 👍 0 🔁 0 💬 0 📌 0
The waiting period would be on resubmitting the same paper though, which may be helpful to prevent authors from spamming the same paper over and over again until they get lucky.
03.02.2026 06:41 — 👍 0 🔁 0 💬 2 📌 0
International Association for Cryptologic Research
The IACR board sent a survey to members last year, and it took us a while to analyze the results and publish findings. You can see them at iacr.org/surveyresults/
03.02.2026 00:24 — 👍 8 🔁 9 💬 2 📌 2
1. In the AIM, the Sigma protocol underlying SQIsign is sound without rewinding, which means we can show that SQIsign is provably secure in the QROM.
2. The CDH and DLOG problem for all SIDH-like key exchanges (M-SIDH, MD-SIDH, binSIDH, terSIDH, etc.) are equivalent in the AIM.
09.01.2026 15:06 — 👍 4 🔁 1 💬 1 📌 0
New paper out! 🎉
We translate the algebraic group model to the (generic) isogeny setting, generalising previous results that were limited to oriented isogenies (we show that any result that holds in the AGAM also holds in the AIM).
Using this model, we obtain two important results:
09.01.2026 15:04 — 👍 12 🔁 3 💬 1 📌 0
It also helps to announce those limits in advance, or communicate them clearly, or NOT delete rebuttals, or...
16.12.2025 13:29 — 👍 1 🔁 0 💬 0 📌 0
This makes more sense than it seems: the time change happens at the same time in both time zones, which means in the UK it’s at 1am rather than 2am.
26.10.2025 17:22 — 👍 2 🔁 0 💬 1 📌 0
The Isogeny Club Season 7 starts today! At 5pm CEST, Bruno Sterner will talk about finding large smooth twins from short lattice vectors. More details at isogeny.club
23.09.2025 07:23 — 👍 10 🔁 7 💬 1 📌 0
The Isogeny Problems
Announcing The Isogeny Problems!
A curated list of the seven foremost unsolved problems in isogeny-based cryptography. Solving one of these profound questions would mark a monumental advance, and as a resolver you'd get eternal honor and epic rewards!
Full list: isogeni.es/problems
15.09.2025 07:43 — 👍 16 🔁 6 💬 1 📌 0
The EU wants to spend your money to assemble a giant mass surveillance machine with little effect on harm against children. Chat Control is not effective, weakens security for all and does not respect privacy. Contact your EU representatives and let them know.
csa-scientist-open-letter.org/Sep2025
09.09.2025 11:24 — 👍 20 🔁 10 💬 0 📌 0
If you're a researcher in cryptography, security, or related areas, please consider signing it too. Signature collection is still open!
09.09.2025 10:41 — 👍 2 🔁 0 💬 0 📌 0
More than 500 researchers have signed an open letter against the dangerous EU proposal on chat control.
The proposal remains ineffective, undoes decades of results in E2E encryption, and threatens the privacy of half a billion citizens.
csa-scientist-open-letter.org/Sep2025
09.09.2025 10:40 — 👍 16 🔁 12 💬 1 📌 0
andrea basso
New somewhat redesigned, somewhat expanded website at andreabasso.com!
If you find any dead links or things not working properly, please let me know
03.09.2025 11:24 — 👍 1 🔁 0 💬 0 📌 0

Abstract. The Learning with Rounding (LWR) problem, introduced as a deterministic variant of Learning with Errors (LWE), has become a promising foundation for post-quantum cryptography. This Systematization of Knowledge (SoK) paper presents a comprehensive survey of the theoretical foundations, algorithmic developments, and practical implementations of LWR-based cryptographic schemes. We introduce LWR within the broader landscape of lattice-based cryptography and post-quantum security, highlighting its advantages such as reduced randomness, improved efficiency, and enhanced side-channel resistance. We explore the evolution of security reductions from LWR to LWE, including recent advances that support practical parameter regimes and address challenges in both bounded and unbounded sample settings. This paper systematically reviews existing LWR-based schemes — including Saber, Lizard, Florete, Espada, Sable, and SMAUG — analyzing their design choices, parameter sets, and performance trade-offs. Furthermore, we examine the impact of LWR on side-channel resistance, failure probabilities, and masking efficiency, demonstrating its suitability for secure and efficient implementations. By consolidating the research spanning theory and practice, this SoK aims to guide future cryptographic design and standardization efforts leveraging LWR.

Image showing part 2 of abstract.
Using Learning with Rounding to Instantiate Post-Quantum Cryptographic Algorithms (Andrea Basso, Joppe W. Bos, Jan-Pieter D'Anvers, Angshuman Karmakar, Jose Maria Bermudo Mera, Joost Renes, Sujoy Sinha Roy, Frederik Vercauteren, Peng Wang, Yuewu Wang, Shicong Zhang, Chenxin Zhong) ia.cr/2025/1382
31.07.2025 14:06 — 👍 4 🔁 3 💬 0 📌 0
Call for Stipends - ASCRYPTO '25
And for For PhD & advanced MSc students!
🌍 Stipends available for students worldwide — thanks to our sponsors!
📋 Apply for stipends here: docs.google.com/forms/d/e/1F...
🖼️ Consider presenting your work in the Latincrypt poster session!
🔗 More info: ascrypto.org/2025/
25.06.2025 15:49 — 👍 2 🔁 2 💬 0 📌 0
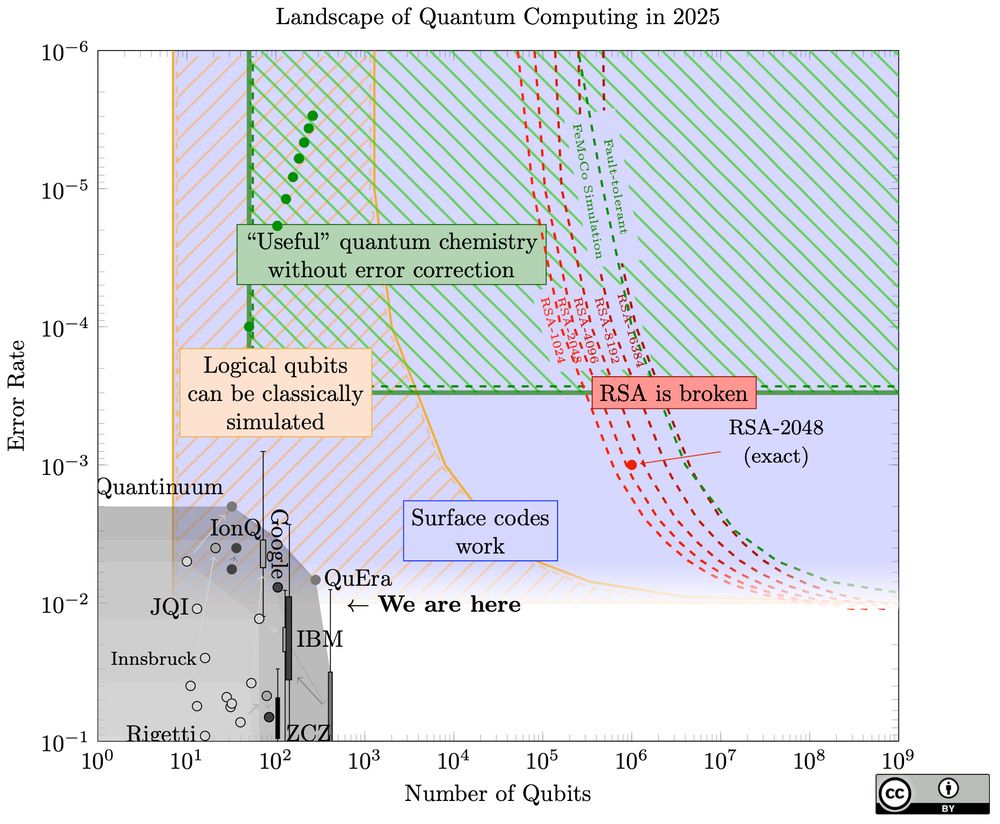
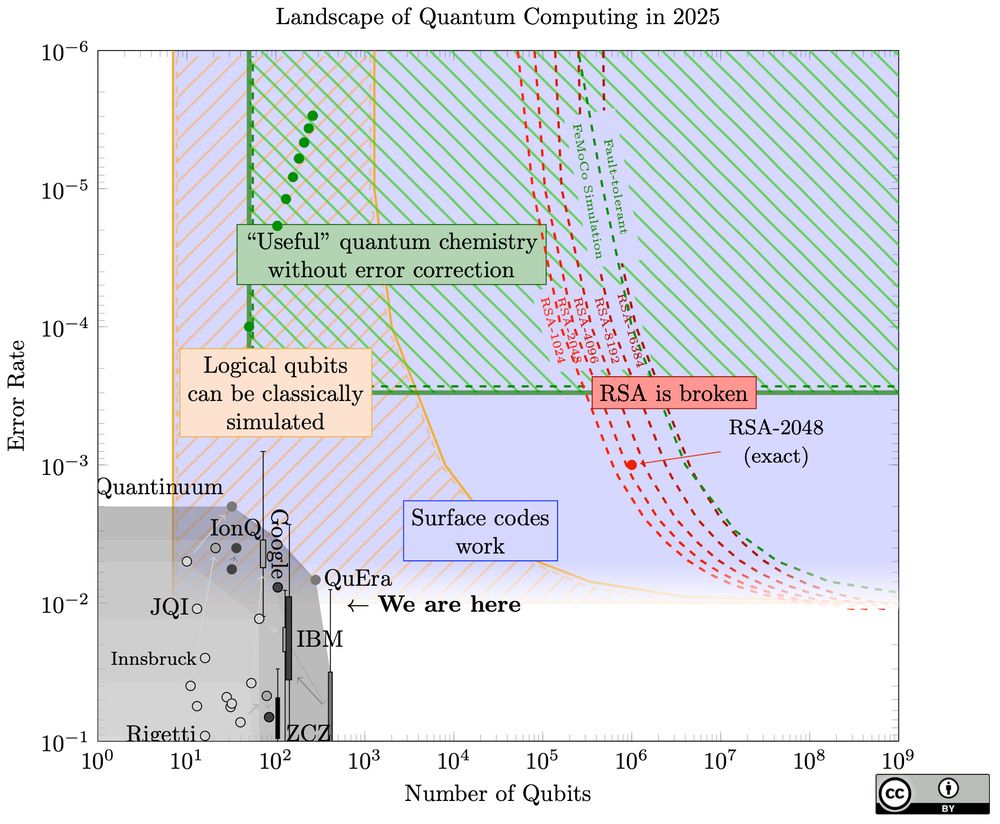
A chart for quantum computers, of number of qubits versus error rate, on a logarithmic scale. Broadly it shows a large gap between current quantum computers in the bottom left, and a curve in the top right of the resources they need to break RSA.
An out-of-schedule update to my quantum landscape chart: sam-jaques.appspot.com/quantum_land..., prompted by
@craiggidney.bsky.social 's new paper: arxiv.org/abs/2505.15917.
A startling jump (20x) in how easy quantum factoring can be!
Also: much improved web design!
19.06.2025 18:52 — 👍 61 🔁 26 💬 3 📌 0
I’m afraid not :(
14.06.2025 06:50 — 👍 0 🔁 0 💬 0 📌 0
We (finally) published all the material from this course on SQIsign, including lecture slides and exercise sheets for the Sage laboratory. Available here: github.com/andreavico/S...
10.06.2025 15:58 — 👍 16 🔁 16 💬 1 📌 0
For any polynomial-time abbiatese A...
(abbiategrassese? abbiatese grasso?)
28.05.2025 07:53 — 👍 1 🔁 0 💬 0 📌 0
Every time I'm writing a paper I always have the same question: is the attacker a person? Is the attacker a they or a it?
27.05.2025 21:35 — 👍 2 🔁 0 💬 1 📌 0
Really cool post on DH!
25.05.2025 14:10 — 👍 1 🔁 0 💬 0 📌 0
Starting in half an hour!
19.05.2025 08:01 — 👍 2 🔁 1 💬 0 📌 0
By 2030 we will all be out of jobs
18.05.2025 19:15 — 👍 0 🔁 0 💬 0 📌 0
👀
18.05.2025 15:00 — 👍 0 🔁 0 💬 0 📌 0
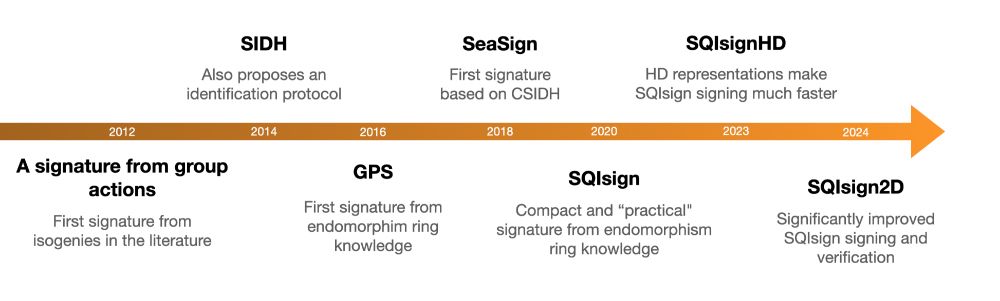
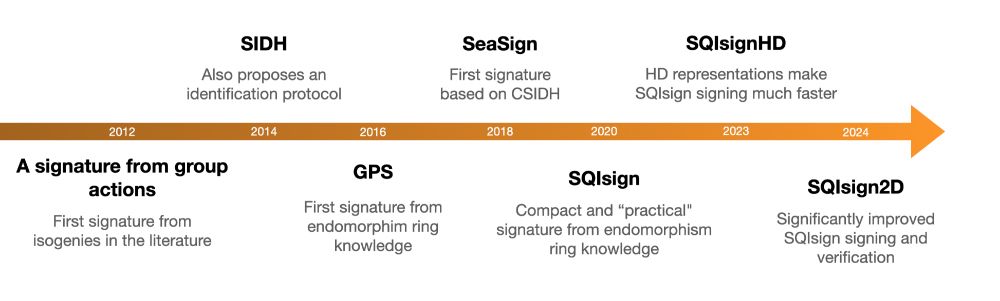
A timeline of isogeny-based signatures over the years:
2012 - A signature from group actions: First signature from
isogenies in the literature
2014 - SIDH: Also proposes an identification protocol
2016 - GPS: First signature from endomorphism ring knowledge
2018 - SeaSign: First signature based on CSIDH
2020 - SQIsign: Compact and “practical" signature from endomorphism ring knowledge
2023 - SQIsignHD: HD representations make SQIsign signing much faster
2024 - SQIsign2D: Significantly improved SQIsign signing and verification
Isogeny-based signatures have consistently had a breakthrough every two years! Let's see what 2026 will bring...
(Well, except for SQIsignHD that came a year too late, but that's probably because of Covid)
18.05.2025 13:50 — 👍 9 🔁 2 💬 3 📌 0
Decrypting Diversity Summit
Decrypting Diversity Summit
Registrations for the Decrypting Diversity Summit are open:
decryptingdiversity.com/registration/
The event's focus is to develop actions to better support underrepresented groups in cryptography while showcasing the exceptional career paths and research contributions of these communities.
15.05.2025 14:34 — 👍 2 🔁 4 💬 1 📌 0
It's somewhat uncertain but probably not. But we'll share the slides, Sage exercises, and other material after the course
17.05.2025 14:58 — 👍 3 🔁 0 💬 0 📌 0
Research Fellow at NTU Singapore.
Interested in privacy-preserving technologies, including pairing-based cryptography and post-quantum cryptography
he/him
ms in cybersecurity @uni-saarland.de
researcher @cispa.de
future phd candidate
trying to understand the world one packet and page at a time. eternally optimistic.
https://alan.chung-ma.com
@purdueece.bsky.social alumn
Daniel Nichanian. Editor in chief of @boltsmag.org (follow us!). Elections, (local) politics, voting rights, criminal justice, and drag race.
Trained journalist, Editor, documentary maker and sports commentator.
Ukraine expert. Numbers nerd.
Almost famous on Xitter!
Coffee donations accepted!
https://ko-fi.com/twmcltd
Lecturer in Maths & Stats at Bristol. Interested in probabilistic + numerical computation, statistical modelling + inference. (he / him).
Homepage: https://sites.google.com/view/sp-monte-carlo
Seminar: https://sites.google.com/view/monte-carlo-semina
☕️ buymeacoffee.com/MAKS22
🇺🇦 PayPal: maksmu24@ukr.net
👀 patreon.com/Maks24
Taking one step at a time in crypto (cryptography and cryptocurrencies both) and privacy
MSc in cybersecurity. Aspiring cryptographer.
interrato.dev
perpetuatheme.com
Trying to be a guitarist, a runner and a good person. Sometimes, I also do cryptography
Post-channel side-quantum guy
To computer scientists Dagstuhl has a special ring: a place to hide away for intensive seminars. The center facilitates research also by its bibliography database dblp and its open access publishing.
Visit https://www.dagstuhl.de to learn more.
Dr. Reza Ebrahimi Atani is an associate professor in the Computer Engineering Department at the University of Guilan and Director of Computer Security Incident Response Teams Research Laboratory.
Same as @thomasforth on X. Gone back to Twitter for now. Quality filter, locations in bios, and polls pls. Leeds, Yorkshire, UK.
Physicist at NIST Boulder, views are my own.
Mathematician at UCLA. My primary social media account is https://mathstodon.xyz/@tao . I also have a blog at https://terrytao.wordpress.com/ and a home page at https://www.math.ucla.edu/~tao/
science journalist | good physics, bad physics, and sometimes ugly physics
Signal: dgaristo.72
Email: digaristo@gmail.com
i write the data-driven politics newsletter Strength In Numbers: gelliottmorris.com/subscribe
wrote a book by the same name wwnorton.com/books/Strength-in-Numbers
polling averages at @fiftyplusone.news
formerly @ 538 & The Economist. email, don't DM, me